NetApp Certified Data Administrator, ONTAP v7.0
Question 1
You have a volume in an SVM that needs to be moved to a different SVM. You do not have room to copy the volume to the other SVM.
Which ONTAP command will accomplish this task?
- A. volume rehost
- B. volume mount
- C. volume modify
- D. volume move
Answer : A
Explanation:
If you have been working with Netapp Clustered Data Ontap for a while now you would no doubt have performed quite a few volume moves. However one limitation of the volume move command was that you couldnt move the volume between storage virtual machines
(SVMs). Starting with Ontap 9 we can now move a volume between Storage Virtual
Machines (SVMs). This is done with the volume rehost command.
References: http://www.sysadmintutorials.com/netapp-ontap-9-volume-rehost/
Question 2
Click the exhibit button.
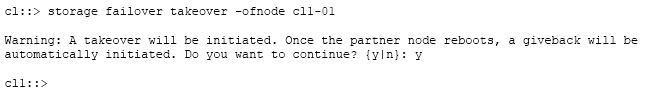
You have a 2-node cluster named cl1 that has separate LIFs on each node for both SAN and NAS traffic. A storage failover takeover process is initiated as shown in the exhibit.
In this scenario, which two statements about the takeover process are true? (Choose two.)
- A. The SAN LIFs on cl1-01 go offline.
- B. The NAS LIFs on cl1-01 automatically migrate to cl1-02.
- C. The NAS LIFs on cl1-01 go offline.
- D. The SAN LIFs on cl1-01 automatically migrate to cl1-02.
Answer : BC
Explanation:
Storage failover takeover -
{ -ofnode {<nodename>|local} - Node to Takeover
This specifies the node that is taken over. It is shut down and its partner takes over its storage.
References:
https://library.netapp.com/ecmdocs/ECMP1196817/html/storage/failover/takeover.html
Question 3
An administrator enabled the iSCSI protocol on an SVM and created a LUN for a Windows
2016 system. After rescan, the LUN is not visible on the host.
Which two steps must the administrator take to solve this problem? (Choose two.)
- A. Create an initiator group (igroup), add the WWPN of the host initiator, and then map the igroup to the LUN.
- B. Disable the ALUA support from the host for the LUN.
- C. Configure the iSCSI service on the Windows 2016 system.
- D. Create an initiator group (igroup), add the iSCSI IQN, and map the igroup to the LUN.
Answer : CD
Explanation:
D: An iSCSI qualified name (IQN) identifier is a worldwide unique name that each iSCSI initiator and iSCSI target must have. The IQN for an iSCSI initiator is available in Microsoft iSCSI Software Initiator or other iSCSI initiators. Typically the IQN is used by the iSCSI target to identify the iSCSI initiator.
Question 4
You are creating the source and destination SVMs for a new SVM disaster recovery relationship.
Which SVM set of subtypes should you choose?
- A. Source SVM default, Destination SVM: default
- B. Source SVM default, Destination SVM: dp-destination
- C. Source SVM default, Destination SVM: sync-dest
- D. Source SVM default, Destination SVM: sync-dest
Answer : B
Explanation:
A destination Storage Virtual Machine (SVM) is an SVM with the dp-destination subtype created for protecting a source SVM that serves data. A destination SVM contains replicated data and configuration of the source SVM.
References: https://library.netapp.com/ecmdocs/ECMP12454817/html/GUID-62D54AB4-
BAE3-49A9-8F43-98DC03BC4602.html
Question 5
Click the Exhibit button.
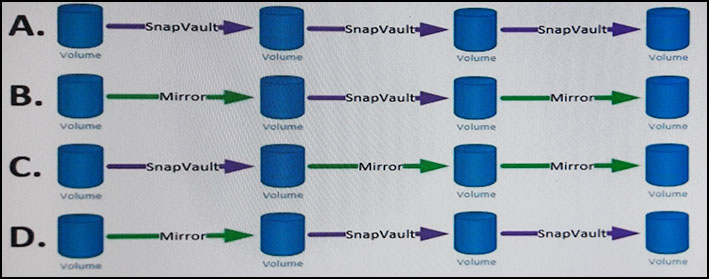
Which two data protection deployment configurations shown in the exhibit are supported?
(Choose two.)
- A. configuration D
- B. configuration C
- C. configuration A
- D. configuration B
Answer : AC
Explanation:
You can use SnapVault to protect a volume SnapMirror destination. You can perform
SnapVault transfers from the volume SnapMirror destination when you want to retain the data for a longer period.
References: https://library.netapp.com/ecmdocs/ECMP1196991/html/GUID-CD48796E-
5FD1-4C2E-B0B2-5773B1A6203C.html
Question 6
Users report that they are unable to connect to home directories stored on a NetApp cluster. You are using Active Directory-based Kerberos authentication.
Which two actions would correct the problem? (Choose two.)
- A. Verify that the CIFS server in running in the SVM.
- B. Verify that the Network Time Protocol service is in sync.
- C. Verify that an Active Directory domain admin account is configured in ONTAP.
- D. Verify that domain tunneling is configured in ONTAP.
Answer : AC
Explanation:
Kerberized NFS in Cluster-Mode for use with Active Directory Pre-requisites include:
Note: The CIFS server is not required for basic NFS Kerberos access, but is required for multiprotocol access or when using AD as an LDAP server for name mappings.
References: https://kb.netapp.com/support/s/article/ka31A0000000uYJQAY/how-to-set-up- kerberized-nfs-in-cluster-mode-with-active-directory?language=en_US
Question 7
Which two features are supported by SnapLock Enterprise but not by SnapLock
Compliance? (Choose two.)
- A. FlexArray
- B. privileged delete
- C. NetApp Volume Encryption (NVE)
- D. SnapMirror
Answer : BD
Explanation:
Features supported by SnapLock Enterprise but not by SnapLock Compliance include:
Note:
Comparison table of SnapLock Enterprise and SnapLock Compliance
The SnapLock Enterprise and the SnapLock Compliance features differ in terms of the options and permissions available for both the features.
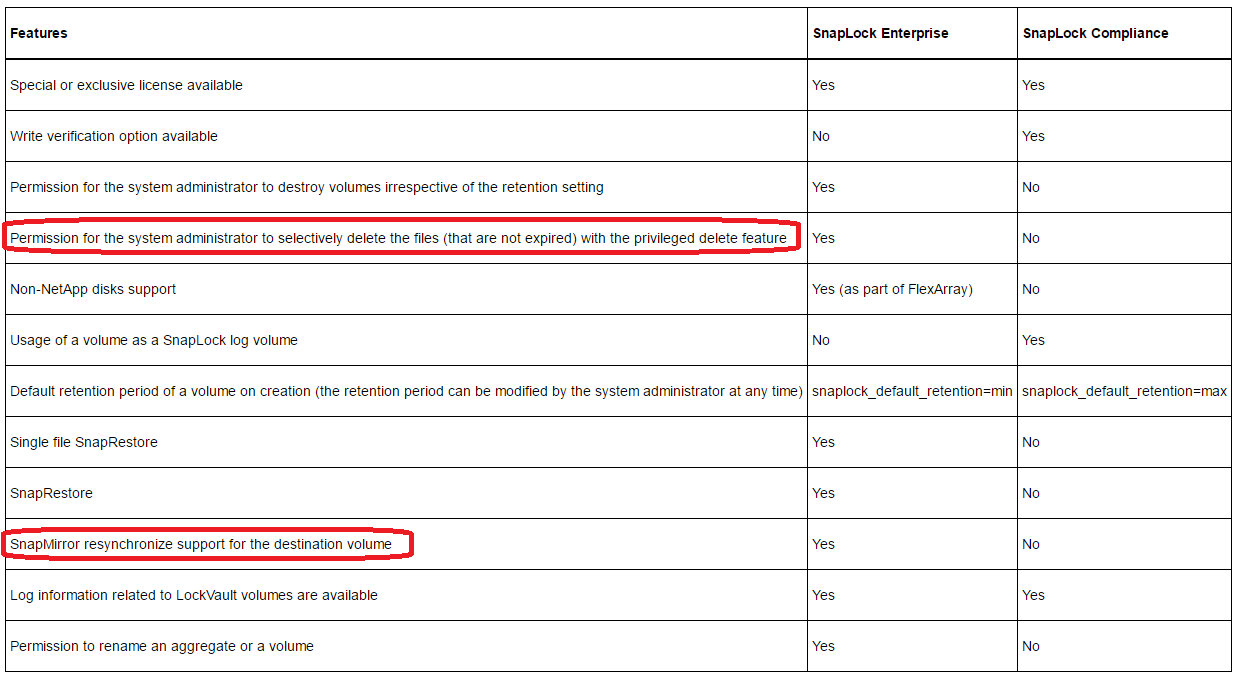
References: https://library.netapp.com/ecmdocs/ECMP1368820/html/GUID-9E05FE59-
BF40-4C22-AD4D-ACBCB552D9A0.html
Question 8
What is an array LUN?
- A. a LUN provisioned in ONTAP that is mounted by a connected host
- B. a LUN provisioned on third-party storage that ONTAP will use as a passthrough LUN
- C. a LUN that is used only as a part of a volume group
- D. a LUN provisioned on third-party storage that ONTAP will use in a RAID group
Answer : A
Explanation:
The Data ONTAP software-based scheme provides ownership control only for storage systems running Data ONTAP; it does not prevent a different type of host from overwriting data in an array LUN owned by a system running Data ONTAP. Therefore, if multiple hosts are accessing array LUNs through the same storage array port, be sure to use LUN security on your storage array to prevent the systems from overwriting each other's array
LUNs.
References: https://library.netapp.com/ecmdocs/ECMP1196986/html/GUID-D5079042-
EA9A-4052-9B00-670B3728FFAA.html
Question 9
You need to duplicate a production LUN for quality assurance testing. The LUN resides in svm_prod and needs to be available in svm_qa. Both SVMs reside on the same cluster.
Which step will accomplish this task?
- A. Issue the lun move command.
- B. Issue the volume rehost command.
- C. Issue the lun copy command.
- D. Issue the volume move command.
Answer : C
Explanation:
Cluster administrators can copy a LUN across Storage Virtual Machines (SVMs) within the cluster by using the lun copy command.
References: http://docs.netapp.com/ontap-9/index.jsp?topic=%2Fcom.netapp.doc.dot-cm- sanag%2FGUID-5B6FA678-31F6-4572-9E9E-B22637BAE911.html
Question 10
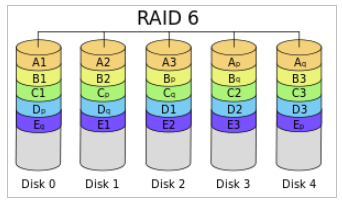
Click the Exhibit button.
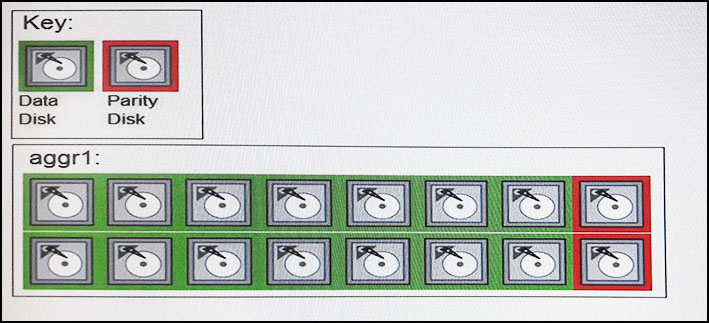
The size of the aggr1 RAID group shown in the exhibit is 8.
What is the RAID type?
- A. RAID-TEC
- B. RAID-DP
- C. RAID4
- D. RAID0
Answer : B
Explanation:
RAID 6 extends RAID 5 by adding another parity block; thus, it uses block-level striping with two parity blocks distributed across all member disks.
Figure: Diagram of a RAID 6 setup, which is identical to RAID 5 other than the addition of a second parity block
Question 11
Which CLI command is used to move epsilon to a new node?
- A. cluster modify
- B. cluster identity modify
- C. cluster setup
- D. storage failover takeover
Answer : A
Explanation:
Reassigning epsilon to another node in the cluster.
Only one node in the cluster can hold epsilon. Epsilon gives the holding node an extra fractional voting weight in the quorum.
Steps -
References: https://library.netapp.com/ecmdocs/ECMP1196798/html/GUID-5FAA5445-
0872-400B-B7AD-B27CEE3D770A.html
Question 12
You have a SnapLock Compliance volume that needs to be replicated to a different cluster at a disaster recovery site.
Which two statements concerning the SnapMirror destination volume are true? (Choose two.)
- A. The destination volume type must be SnapLock Enterprise.
- B. The destination volume type must be SnapLock Compliance.
- C. The destination cluster does not require a SnapLock license.
- D. The destination cluster requires a SnapLock license.
Answer : BD
Explanation:
B: To create an end-to-end relationship between SnapLock Compliance volumes by using
SnapMirror, you need to create both the source and the destination volumes as SnapLock
Compliance volumes and then initialize the mirroring relationship by using the snapmirror initialize command. The other commands you use differ depending on whether you are creating a volume SnapMirror relationship for a traditional volume or a FlexVol volume.
D: A SnapLock license entitles you to use both SnapLock Compliance mode and SnapLock
Enterprise mode. SnapLock licenses are issued on a per-node basis. You must install a license for each node that hosts a SnapLock aggregate.
References: https://library.netapp.com/ecmdocs/ECMP1196889/html/GUID-8ACE3CAB-
D338-4AFC-A530-0D0FEC3B9F94.html
https://library.netapp.com/ecm/ecm_download_file/ECMLP2507748
Question 13
Click the Exhibit button.
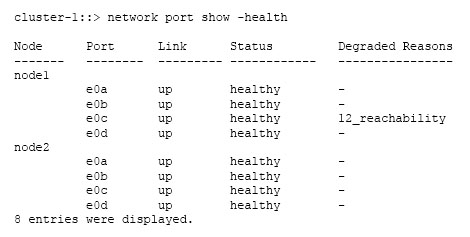
While reviewing the port health shown in the exhibit, you notice that port e0c on node1 is degraded.
What would cause this problem?
- A. The port is not plugged into a switch.
- B. The port is in the wrong broadcast domain.
- C. The port does not have an IP address.
- D. The port has been flapping.
Answer : B
Explanation:
L2 reachability health monitor: Monitors whether all ports configured in the same broadcast domain have L2 reachability to each other.
This health monitor reports L2 reachability issues in all IPspaces; however, it marks only the ports in the cluster IPspace as degraded.
Question 14
Click the Exhibit button.
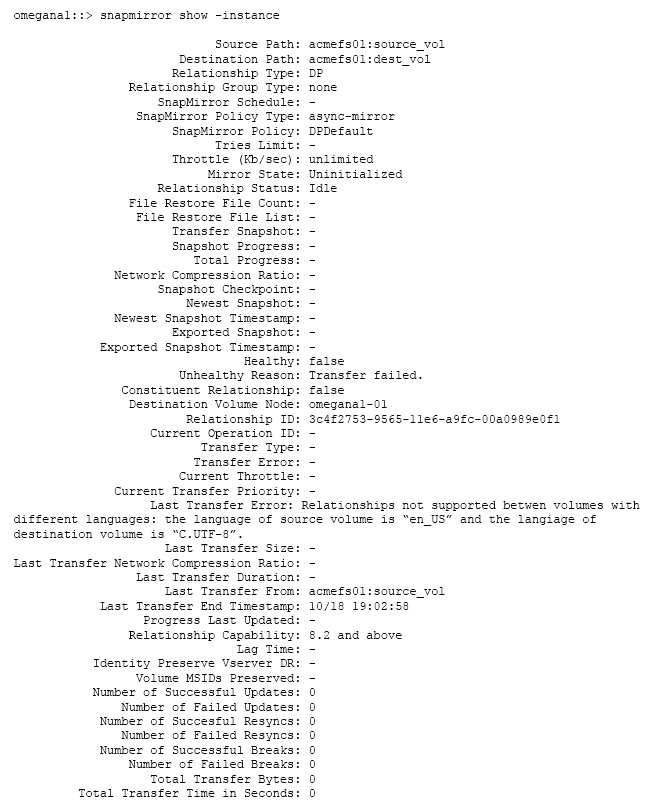
You create a new SnapMirror relationship, but is fails to initialize. The SnapMirror relationship is configured as shown in the exhibit.
How would you solve this problem?
- A. Re-create the destination volume as C.UTF-8.
- B. Re-create the destination volume as en_US.
- C. Change the language on the source volume to en_US.
- D. Change the language on the destination volume to C.UTF-8.
Answer : D
Explanation:
Cause: The language setting in the source Vserver is not the same as the language setting in the destination Vserver.
Resolution: The only way to resolve this issue is to create a destination Vserver with the same language setting as the source Vserver.
References:
https://kb.netapp.com/support/s/article/ka11A000000167gQAA/troubleshooting-workflow- snapmirror-initialization-failures?language=en_US
Question 15
Click the Exhibit button.
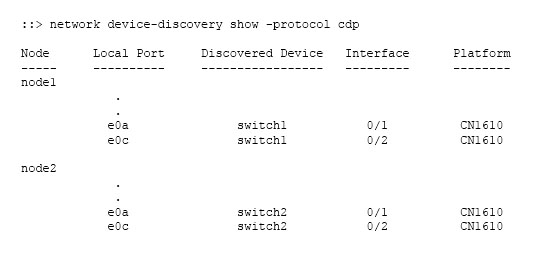
Referring to the exhibit, which two statements about the connectivity from the 2-node cluster to the cluster interconnects are true? (Choose two.)
- A. The CN1610 switches were discovered by using Cisco CDP.
- B. The nodes are cabled correctly.
- C. The nodes are cabled incorrectly.
- D. The CN1610 switches were discovered by using LLDP.
Answer : AC
Explanation:
From the exhibit we see that cdp is used.
Cabling the private cluster interconnect for NetApp CN1610 switches.
Steps -
References: https://library.netapp.com/ecmdocs/ECMP1197116/html/GUID-3F4B53E3-
C5D4-40D8-ABF3-4FD8AFD6D10D.html