CompTIA Cloud+ (CV0-002) v1.0
Question 1
A cloud administrator has deployed a new all-flash storage array with deduplication and compression enabled, and moved some of the VMs into it. The goal was to achieve 4:1 storage efficiency while maintaining sub-millisecond latency. Which of the following results would BEST suit the requirements?
- A. Compression 1:1 Deduplication 4:1 Overall savings 4:1 Average latency 1.0ms
- B. Compression 1.5:1 Deduplication 1.8:1 Overall savings 2.2:1 Average latency 600us
- C. Compression 1.3:1 Deduplication 3.1:1 Overall savings 4.3:1 Average latency 900us
- D. Compression 1.8:1 Deduplication 2.7:1 Overall savings 4.2:1 Average latency 1.2ms
Answer : A
Question 2
A newly established CSP allows for drive shipping to upload new data into the environment. Sensitive data on 40TB of storage needs to be transferred within one week. Which of the following is the MOST efficient and secure method for shipment of the data to the CSP with minimal downtime?
- A. Create a VPN between the sites and schedule data transfer during non-business hours.
- B. Copy the data to encrypted drives and use the CSP-certified shipping provider.
- C. Compress and SFTP the data to the CSP.
- D. Move the data to encrypted drives and use the CSP-certified shipping provider.
Answer : D
Question 3
A manufacturing company's current security policy mandates PII is not stored in the SaaS solution. Which of the following configuration controls should be used to block sensitive information from being stored in the SaaS solution?
- A. Implement file-level encryption.
- B. Implement a network ACL.
- C. Implement an IPS.
- D. Implement content filtering.
Answer : B
Question 4
A new application with availability SLA requirements of 99.99% has been deployed in a cloud. For a test spanning a month, which of the following unavailability times would mean the test was successful? (Select two).
- A. 1 minute
- B. 4 minutes
- C. 10 minutes
- D. 30 minutes
- E. 60 minutes
Answer : AB
Question 5
A company's security policy requires full disk encryption on all clients with preboot enabled. The encryption server is hosted, and the requirement is to push an update to all endpoints. Which of the following is the BEST method to test and apply the update with minimal disruption to end users?
- A. Access the API of the encryption server, develop a custom script, and then update all endpoints.
- B. Access the web UI portal of the encryption server, apply the update to the test group, validate, and then update all endpoints.
- C. Add the update to the standard desktop configuration image, apply the update to a test VM, and then reimage clients.
- D. Access the web UI of the encryption server and disable preboot, apply the update, test, and then deploy the update to all endpoints.
Answer : B
Question 6
A technician receives a report of system utilization:
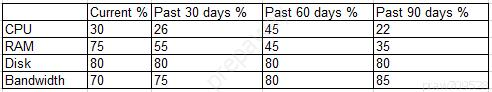
Which of the following additional resources should the technician add FIRST given the trend data shown above?
- A. CPU
- B. Disk
- C. Bandwidth
- D. RAM
Answer : B
Question 7
A cloud architect is tasked with isolating traffic between subnets in an IaaS platform. The networks should be able to statefully communicate with each other.
Given this scenario, which of the following should the architect implement?
- A. Configure security groups.
- B. Configure HIPS policies.
- C. Configure IDS policies.
- D. Configure a network ACL.
Answer : A
Question 8
A cloud administrator is provisioning several user accounts that have administrator rights to assets using JSON within an IaaS cloud platform. The administrator is required to configure "alternateג€ settings using the API. Given this scenario, which of the following elements would allow the administrator to meet these requirements in the JSON file?
- A. Statement
- B. Effect
- C. Resource
- D. Condition
Answer : A
Question 9
Before doing a change on a VM, a systems administrator wants to ensure there is an easy and fast way to rollback if needed. The change and testing should take approximately two hours. Which of the following is the EASIEST way to meet this requirement?
- A. Create a snapshot on the hypervisor.
- B. Make an on-demand, incremental backup to a VTL.
- C. Make an on-demand, full backup to a secondary location.
- D. Create a snapshot on a remote storage array.
Answer : A
Question 10
The CSA needs to install a patch on 58 virtual server instances during the Friday evening maintenance window. Which of the following is the MOST efficient way to get the patches installed?
- A. Use the patch management tool to automate and orchestrate the patch installation.
- B. Use a security vulnerability scanning tool to apply the patch automatically.
- C. Schedule the patch to install from a remote file server upon server reboot.
- D. Connect the server instances to the Internet to download the patch automatically.
Answer : A
Question 11
A recent advertisement campaign has increased traffic to an e-commerce application that is hosted within a public cloud environment. Customers are reporting that it takes too long to load their pages and submit orders. A cloud administrator looks at the metrics from the environment and sees high utilization of the CPU and memory resources. The cloud provider offers several preconfigured sizes for server template: x-small, small, medium, large, x-large, and 2x-large.
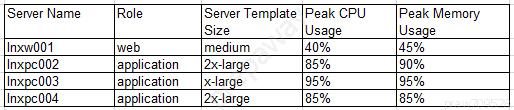
Given an expected increase in workload, which of the following is the BEST solution to improve application performance?
- A. Change the server template size for Inxpc003 to 2x-large.
- B. Provision additional Inxpc servers using the 2x-large template.
- C. Add memory to Inxpc002, Inxpc003, and Inxpc003.
- D. Change the role of Inxw001 from web to application.
Answer : A
Question 12
A company wants to leverage a SaaS provider for its back-office services, and security is paramount. Which of the following solutions should a cloud engineer deploy to BEST meet the security requirements?
- A. Firewall
- B. IPS/IDS
- C. Proxy gateway
- D. CASB
Answer : D
Question 13
A company upgraded a hosted vulnerability scanner to the latest version, and now tickets are not being created to assign critical vulnerabilities. After confirming the ticketing issue, all the scanning services are confirmed to be running on the VM. Which of the following is the MOST likely cause and best method to fix the issue?
- A. There was an IP change to the VM. Make changes to the server properties.
- B. The upgrade has a bug Reboot the server and attempt the upgrade again.
- C. The vulnerability scanner is on a different subnet. Open the ports, and it will reconnect.
- D. There is an application compatibility issue. Roll back to the previous working backup.
Answer : D
Question 14
A system's application servers need to be patched. The requirements for maintenance work are as follows:
✑ System downtime is not allowed.
✑ The application server in use must be in the sane patch status.
✑ System performance must be maintained during patching work.
✑ Testing after patching must be done before the application server is in use.
✑ If any trouble occurs, recover the previous version in ten minutes.
Which of the following methodologies should be selected?
- A. Rolling update
- B. Patching directly
- C. Blue-green deployment
- D. Three staging environments
Answer : D
Question 15
A software development company is building cloud-ready applications and needs to determine the best approach for releasing software. Which of the following approaches should be used?
- A. Perform QA, develop, test, and release to production
- B. Test, perform QA, develop, and release to production
- C. Develop, perform QA, test, and release to production
- D. Develop, test, perform QA, and release to production
Answer : D