CompTIA Advanced Security Practitioner (CASP) CAS-003 v1.0
Question 1
A Chief Information Officer (CIO) publicly announces the implementation of a new financial system. As part of a security assessment that includes a social engineering task, which of the following tasks should be conducted to demonstrate the BEST means to gain information to use for a report on social vulnerability details about the financial system?
- A. Call the CIO and ask for an interview, posing as a job seeker interested in an open position
- B. Compromise the email server to obtain a list of attendees who responded to the invitation who is on the IT staff
- C. Notify the CIO that, through observation at events, malicious actors can identify individuals to befriend
- D. Understand the CIO is a social drinker, and find the means to befriend the CIO at establishments the CIO frequents
Answer : D
Question 2
A recent assessment identified that several usersג€™ mobile devices are running outdated versions of endpoint security software that do not meet the companyג€™s security policy. Which of the following should be performed to ensure the users can access the network and meet the companyג€™s security requirements?
- A. Vulnerability assessment
- B. Risk assessment
- C. Patch management
- D. Device quarantine
- E. Incident management
Answer : C
Question 3
A company suspects a web server may have been infiltrated by a rival corporation. The security engineer reviews the web server logs and finds the following: ls -l -a /usr/heinz/public; cat ./config/db.yml
The security engineer looks at the code with a developer, and they determine the log entry is created when the following line is run: system ("ls -l -a #{path}")
Which of the following is an appropriate security control the company should implement?
- A. Restrict directory permissions to read-only access.
- B. Use server-side processing to avoid XSS vulnerabilities in path input.
- C. Separate the items in the system call to prevent command injection.
- D. Parameterize a query in the path variable to prevent SQL injection.
Answer : C
Question 4
A Chief Information Security Officer (CISO) is reviewing the results of a gap analysis with an outside cybersecurity consultant. The gap analysis reviewed all procedural and technical controls and found the following:
✑ High-impact controls implemented: 6 out of 10
✑ Medium-impact controls implemented: 409 out of 472
✑ Low-impact controls implemented: 97 out of 1000
The report includes a cost-benefit analysis for each control gap. The analysis yielded the following information:
✑ Average high-impact control implementation cost: $15,000; Probable ALE for each high-impact control gap: $95,000
✑ Average medium-impact control implementation cost: $6,250; Probable ALE for each medium-impact control gap: $11,000
Due to the technical construction and configuration of the corporate enterprise, slightly more than 50% of the medium-impact controls will take two years to fully implement. Which of the following conclusions could the CISO draw from the analysis?
- A. Too much emphasis has been placed on eliminating low-risk vulnerabilities in the past
- B. The enterprise security team has focused exclusively on mitigating high-level risks
- C. Because of the significant ALE for each high-risk vulnerability, efforts should be focused on those controls
- D. The cybersecurity team has balanced residual risk for both high and medium controls
Answer : C
Question 5
After investigating virus outbreaks that have cost the company $1000 per incident, the companyג€™s Chief Information Security Officer (CISO) has been researching new antivirus software solutions to use and be fully supported for the next two years. The CISO has narrowed down the potential solutions to four candidates that meet all the companyג€™s performance and capability requirements:
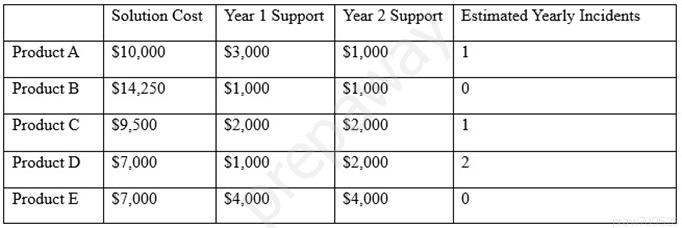
Using the table above, which of the following would be the BEST business-driven choice among the five possible solutions?
- A. Product A
- B. Product B
- C. Product C
- D. Product D
- E. Product E
Answer : D
Question 6
A financial consulting firm recently recovered from some damaging incidents that were associated with malware installed via rootkit. Post-incident analysis is ongoing, and the incident responders and systems administrators are working to determine a strategy to reduce the risk of recurrence. The firmג€™s systems are running modern operating systems and feature UEFI and TPMs. Which of the following technical options would provide the MOST preventive value?
- A. Update and deploy GPOs
- B. Configure and use measured boot
- C. Strengthen the password complexity requirements
- D. Update the antivirus software and definitions
Answer : D
Question 7
A company monitors the performance of all web servers using WMI. A network administrator informs the security engineer that web servers hosting the companyג€™s client-facing portal are running slowly today. After some investigation, the security engineer notices a large number of attempts at enumerating host information via
SNMP from multiple IP addresses. Which of the following would be the BEST technique for the security engineer to employ in an attempt to prevent reconnaissance activity?
- A. Install a HIPS on the web servers
- B. Disable inbound traffic from offending sources
- C. Disable SNMP on the web servers
- D. Install anti-DDoS protection in the DMZ
Answer : A
Question 8
One of the objectives of a bank is to instill a security awareness culture. Which of the following are techniques that could help to achieve this? (Choose two.)
- A. Blue teaming
- B. Phishing simulations
- C. Lunch-and-learn
- D. Random audits
- E. Continuous monitoring
- F. Separation of duties
Answer : BE
Question 9
The risk subcommittee of a corporate board typically maintains a master register of the most prominent risks to the company. A centralized holistic view of risk is particularly important to the corporate Chief Information Security Officer (CISO) because:
- A. IT systems are maintained in silos to minimize interconnected risks and provide clear risk boundaries used to implement compensating controls
- B. risks introduced by a system in one business unit can affect other business units in ways in which the individual business units have no awareness
- C. corporate general counsel requires a single system boundary to determine overall corporate risk exposure
- D. major risks identified by the subcommittee merit the prioritized allocation of scare funding to address cybersecurity concerns
Answer : B
Question 10
An insurance company has two million customers and is researching the top transactions on its customer portal. It identifies that the top transaction is currently password reset. Due to users not remembering their secret questions, a large number of calls are consequently routed to the contact center for manual password resets. The business wants to develop a mobile application to improve customer engagement in the future, continue with a single factor of authentication, minimize management overhead of the solution, remove passwords, and eliminate to the contact center. Which of the following techniques would BEST meet the requirements? (Choose two.)
- A. Magic link sent to an email address
- B. Customer ID sent via push notification
- C. SMS with OTP sent to a mobile number
- D. Third-party social login
- E. Certificate sent to be installed on a device
- F. Hardware tokens sent to customers
Answer : CE
Question 11
A security engineer has implemented an internal user access review tool so service teams can baseline user accounts and group memberships. The tool is functional and popular among its initial set of onboarded teams. However, the tool has not been built to cater to a broader set of internal teams yet. The engineer has sought feedback from internal stakeholders, and a list of summarized requirements is as follows:
✑ The tool needs to be responsive so service teams can query it, and then perform an automated response action.
✑ The tool needs to be resilient to outages so service teams can perform the user access review at any point in time and meet their own SLAs.
✑ The tool will become the system-of-record for approval, reapproval, and removal life cycles of group memberships and must allow for data retrieval after failure.
Which of the following need specific attention to meet the requirements listed above? (Choose three.)
- A. Scalability
- B. Latency
- C. Availability
- D. Usability
- E. Recoverability
- F. Maintainability
Answer : BCE
Question 12
The board of a financial services company has requested that the senior security analyst acts as a cybersecurity advisor in order to comply with recent federal legislation. The analyst is required to give a report on current cybersecurity and threat trends in the financial services industry at the next board meeting. Which of the following would be the BEST methods to prepare this report? (Choose two.)
- A. Review the CVE database for critical exploits over the past year
- B. Use social media to contact industry analysts
- C. Use intelligence gathered from the Internet relay chat channels
- D. Request information from security vendors and government agencies
- E. Perform a penetration test of the competitorג€™s network and share the results with the board
Answer : AD
Question 13
The Chief Information Security Officer (CISO) has asked the security team to determine whether the organization is susceptible to a zero-day exploit utilized in the banking industry and whether attribution is possible. The CISO has asked what process would be utilized to gather the information, and then wants to apply signatureless controls to stop these kinds of attacks in the future. Which of the following are the MOST appropriate ordered steps to take to meet the CISOג€™s request?
- A. 1. Perform the ongoing research of the best practices 2. Determine current vulnerabilities and threats 3. Apply Big Data techniques 4. Use antivirus control
- B. 1. Apply artificial intelligence algorithms for detection 2. Inform the CERT team 3. Research threat intelligence and potential adversaries 4. Utilize threat intelligence to apply Big Data techniques
- C. 1. Obtain the latest IOCs from the open source repositories 2. Perform a sweep across the network to identify positive matches 3. Sandbox any suspicious files 4. Notify the CERT team to apply a future proof threat model
- D. 1. Analyze the current threat intelligence 2. Utilize information sharing to obtain the latest industry IOCs 3. Perform a sweep across the network to identify positive matches 4. Apply machine learning algorithms
Answer : C
Question 14
A software development team is conducting functional and user acceptance testing of internally developed web applications using a COTS solution. For automated testing, the solution uses valid user credentials from the enterprise directory to authenticate to each application. The solution stores the username in plain text and the corresponding password as an encoded string in a script within a file, located on a globally accessible network share. The account credentials used belong to the development team lead. To reduce the risks associated with this scenario while minimizing disruption to ongoing testing, which of the following are the BEST actions to take? (Choose two.)
- A. Restrict access to the network share by adding a group only for developers to the shareג€™s ACL
- B. Implement a new COTS solution that does not use hard-coded credentials and integrates with directory services
- C. Obfuscate the username within the script file with encoding to prevent easy identification and the account used
- D. Provision a new user account within the enterprise directory and enable its use for authentication to the target applications. Share the username and password with all developers for use in their individual scripts
- E. Redesign the web applications to accept single-use, local account credentials for authentication
Answer : AB
Question 15
A security consultant is attempting to discover if the company is utilizing databases on client machines to store the customer data. The consultant reviews the following information:
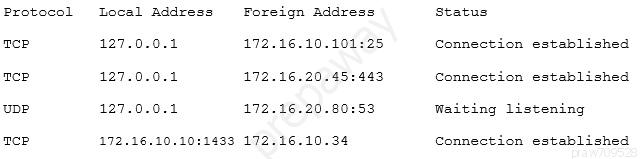
Which of the following commands would have provided this output?
- A. arp -s
- B. netstat -a
- C. ifconfig -arp
- D. sqlmap -w
Answer : B