IBM Security Guardium V10.0 Administration v6.0
Question 1
A Guardium administrator manages portal user synchronization by using a Central
Manager.
When a change is made on the Central Manager such as, for example, adding a Guardium user to a Guardium group, how long should be allowed for the update to be synced with the managed units in a fully working environment?
- A. 0minutes
- B. 15 minutes
- C. 30 minutes
- D. 60 minutes
Answer : D
Question 2
Guardium reports are showing multiple records with client ip as 0.0.0.0. Users are unable to identify which client the connections came from. The Guardium administrator has identified that the databases are using encryption.
Which column can the administrator add that would help users to better identify the client?
- A. Client OS
- B. Client MAC
- C. Access ID
- D. Analyzed Client IP
Answer : B
Question 3
A Guardium administrator is preparing a command to install Configuration Auditing System
(CAS) on a Linux server using the command line method. Which parameter is required?
- A. dir
- B. tapip
- C. java-home
- D. sqlguardip
Answer : D
Question 4
During the initial phase of the Guardium deployment, the Guardium administrator wants to figure out an ideal time period to purge data from the appliance based on the data load.
Which predefined Guardium report(s) allows the administrator to determine the current database disk usage of the Guardium Appliance?
- A. Disk UtiI report
- B. Aggregation/Archive log
- C. DB Server throughput report
- D. Buff Usage Monitor and System Monitor reports
Answer : D
Question 5
AGuardium administrator has rebuilt an appliance, and wants nowto restore a backup image of the entire database, audit data, and all definitions from Data backup.Which CLI command should the administrator use to accomplish this?
- A. restore config
- B. restore system
- C. restore pre-patch-backup
- D. restore certificate sniffer backup
Answer : B
Question 6
Auditors request a report of all unsuccessful login attempts to a database monitored by
Guardium. How should a Guardium administrator create such a report?
- A. Add a failed login rule to the policy.
- B. Create a failed login query and report using access domain in Guardium.
- C. Create a failed login query and report using exceptions domain in Guardium.
- D. Create a failed login query and report using application data domain in Guardium.
Answer : C
Question 7
In a centrally managed environment, while executing the report 'Enterprise Buffer Usage
Monitor', a Guardium administrator gets an empty report. Why is the report empty?
- A. Sniffers are not running on the Collectors.
- B. The report is not executed with a remote source on the Collector.
- C. The report is not executed with a remote source on the Aggregator.
- D. Correct custom table upload is not scheduled on the Central Manager.
Answer : C
Question 8
A Guardium administrator observes certain changes to the configuration and policies. How would the administrator identify the changes that were made and who made them?
- A. Review the Audit Process Log report.
- B. Review the sniffer buffer usage report.
- C. Review the /var/log/messages log file.
- D. Review the results of 'Detailed Guardium User Activity' report.
Answer : D
Question 9
AGuardium administrator is using the Classification, Entitlement and Vulnerability assessment features of the product. Which of the following are correct with regards to these features? (Select two.)
- A. Vulnerability Assessment reports are populated to the Guardium appliance via S-TAP.
- B. Classification for databases and files use the same mechanisms and patterns to search for sensitive data.
- C. Entitlement reports are predefined database privilege reports and are populated to the Guardium appliance via S-TAP.
- D. Vulnerability Assessment identifies and helps correct security vulnerabilities and threats in the database infrastructures.
- E. The classification feature discovers sensitive assets including credit card numbers or national card numbers from various data sources.
Answer : D,E
Question 10
A Guardium administrator must configure real time policy alerts to be sent to a remote
SIEM for every SQL statement run on a sensitive object. There is no requirement for the data to be viewed or reported on in the Guardium appliance.
Which policy action would achieve that task and store the least amount of data in the
Guardium internal database?
- A. Log Only
- B. Alert Only
- C. Alert Daily
- D. Alert Per Match
Answer : C
Question 11
An administrator previously had an issue with a Guardium system. This was resolved with the assistance from the IBM Guardium support team, who provided the shell script, a CLI command and the encrypted key to execute the uploaded shell script.
Which CLI command should the administrator use to review the commands that were previously run?
- A. fjieserver
- B. support execute showlog
- C. show log external state
- D. support must_gather system_db_info
Answer : B
Question 12
A Guardium administrator noticed that while the data activity monitoring is working fine, the
Guardium appliance is slower than usual. The administrator wants to check the current
CPU load of the Guardium appliance.
Which predefined Guardium report(s) allows the administrator to determine the current system CPU load of the Guardium Appliance?
- A. CPU Util report
- B. CPU Tracker report
- C. Unit summary and CPU Util report
- D. Buff Usage Monitor and System monitor report
Answer : D
Question 13
A company wants to deploy S-TAPs for 2 groups of database servers located in 2 different data centers. The current set of Collectors are fully utilized. The Aggregators and Central
Manager can handle more load.
What should a Guardium administrator recommend?
- A. Deploy 2 new Collectors, 1 in each data center.
- B. Connect S-TAPs directly to Aggregators to avoid network latency.
- C. Connect S-TAPs directly to the Central Manager to avoid network latency.
- D. Deploy 2 new Collectors in the third data center located in between the 2 data centers.
Answer : A
Question 14
A Guardium administrator needs to install and configure a physical appliance to ensure network redundancy. Which port should the administrator use to configure IP teaming
(bonding)?
- A. eth1 only
- B. eth2 only
- C. eth3 only
- D. any port
Answer : D
Question 15
The guard_tap.ini of a UNIX S-TAP is configured with the following parameters:
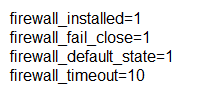
The collector that this S-TAP is sending data to has become unavailable and there is no failover option configured. A Guardium administrator must communicate the impact of this outage to users of the monitored database.
What should the administrator advise is the expected behavior for a database session?
- A. The session will not experience any latency or termination.
- B. No SQL can be executed and after 10 seconds the session will be terminated.
- C. in the first 10 seconds of the session SQL can be executed, then the session is terminated.
- D. in the first 10 seconds of the session no SQL can be executed, then the session will work as normal.
Answer : C