70-685 v57.1
Question 1
The sales users that were part of the VPN server pilot project report that they can no longer establish VPN connections to the internal network.
You need to ensure that all authorized users can establish VPN connections to the internal network.
What should you request a domain administrator to do?
- A. Enable auto-renewal for certificates.
- B. Increase the lifetime of the Kerberos user ticket.
- C. Increase the lifetime of the Kerberos service ticket.
- D. Increase the certification validity period for the computer certificate template.
Answer : A
Question 2
Portable computer users report that they can use Internet Explorer to browse Internet Web sites only when they are connected to the company network.
You need to ensure that portable computer users can access Internet Web sites from wherever they connect.
What should you do?
- A. Instruct the users to configure static IPv4 settings.
- B. Instruct the users to configure automatic IPv4 settings.
- C. Request that a domain administrator link GPO-IE to Active Directory site objects.
- D. Request that a domain administrator create a new GPO that modifies the Internet Explorer Maintenance settings, and then link the new GPO to the Users OUs.
Answer : C
Question 3
A new print device is installed on Floor 1 and shared on Print1.
Users report that when they search Active Directory for printers on Floor 1, the new shared printer is missing. All other shared printers on Floor 1 appear.
The help desk reports that users can manually connect to the shared printer.
You need to ensure that the new shared printer is displayed when users search for printers on Floor 1.
What should you do?
A. Modify the permissions of the printer.
B. Configure a network location for the printer.
C. Request that a domain administrator modify the Active Directory site configuration.
D. Request that a domain administrator modify the GPO that is linked to each departmental
OU.
Answer : B
Topic 8, Fourth Coffee
You are an enterprise desktop support technician for Fourth Coffee.
The network contains a single domain named fourthcoffee.com.
Physical Environment
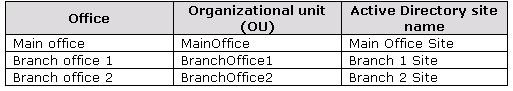
The company has three offices. The offices are configured as shown in the following table.
Question 4
Users in branch office 2 map drives to shared folders on SRV1.
The users report that they cannot access files in the shared folders when the WAN link between branch office 2 and the main office is unavailable. When they attempt to access the files, they are prompted to enter their credentials but are denied access.
You need to ensure that the users can access the shared folders if the WAN link fails.
What should you do?
- A. Instruct a desktop support technician to configure Offline Files on the Windows 7 computers.
- B. Instruct a desktop support technician to configure BranchCache on the Windows 7 computers.
- C. Request that a domain administrator deploy a domain controller in branch office 2.
- D. Request that a domain administrator enable Universal Group Membership Caching for branch office 2.
Answer : B
Explanation:
changed answer from A. to B.
You should use BranchCache in distributed mode and not offline files.
Offline files are for single-user files and this question specifies it's a shared folder.
Question 5
The help desk reports that the new computers experience intermittent failures that generate stop errors.
You need to collect all the critical errors from the new computers.
What should you configure?
- A. a boot configuration data (BCD) store
- B. debugging information
- C. event subscriptions
- D. the system protection settings
Answer : C
Question 6
The application support team reports that the App1 data of some users is not saved to
AppServer1. The team reports that the users deleted the mapped drive.
You need to prevent the users from deleting the mapped drive.
Which settings should you request be modified in the APP1Deploy GPO?
- A. Administrative Templates
- B. AppLocker
- C. Group Policy Preferences
- D. Software Restriction Policies
Answer : C
Explanation:
A. Administrative Templates -
The Administrative Template files allow you to configure and manage registry-based Group
Policy settings.
They are Unicode text files with the extension .adm in Windows XP with SP2 and Windows
Server 2003 with SP1, and XML files with the extensions .admx and .adml in Windows
Vista and later versions of Windows.
Standard Administrative Templates are deployed with your Windows operating systems.
Administrative Templates display the registry settings that you can apply to your users' computers in your GPOs. Information in the templates populates the administrative interface in Group Policy Object Editor, which you use to set secure registry-based policy information.
A number of standard templates automatically populate the Group Policy Object Editor, and you can add or remove templates later. Developers can create custom templates as needed.
C. Group Policy Preferences -
You can use Group Policy preferences to better deploy and manage operating system and application settings.
Group Policy preferences enable IT professionals to configure, deploy, and manage operating system and application settings they previously were not able to manage using
Group Policy. Examples include mapped drives, scheduled tasks, and Start menu settings.
For many types of operating system and application settings, using Group Policy preferences is a better alternative to configuring them in Windows images or using logon scripts.
Group Policy preferences can be used to implement settings which are preferred but not mandatory. This enables IT professionals to deploy software (including Internet Explorer 8) in a standardized initial configuration and still permit users to customize some aspects to their liking.
Question 7
VPN users report that they cannot access shared resources in the branch offices. They can access shared resources in the main office.
Users in the main office report that they can access shared resources in the branch offices.
You need to ensure that the VPN users can access shared resources in the branch offices.
What should you request?
A. that a change be made to the routing table on VPN1
B. that VPN1 be configured to support PPTP-based VPN connections
C. that the routers between the main office and the branch offices be reconfigured
D. that a DNS record for servers in the branch offices be added to the Internet DNS zone for fourthcoffee.com
Answer : A
Topic 9, Wingtip Toys
You are an enterprise desktop support technician for Wingtip Toys. Wingtip Toys has two
offices.
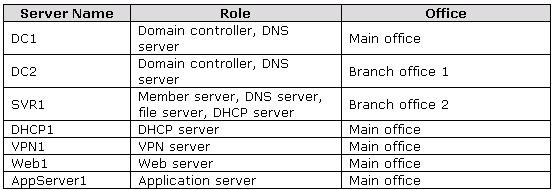
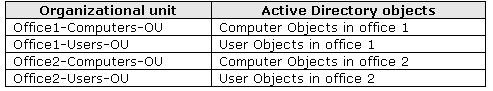
Active Directory Configuration
The network contains a single Active Directory domain. An Active Directory site exists for
each office. The network contains the organizational units (OUs) that are shown in the
following table.
Question 8
You deploy App1 on a test Windows 7 computer and notice that it fails to run.
You need to ensure that App1 runs on Windows 7 computers.
What should you do?
- A. Digitally sign App1.
- B. Develop and deploy a shim for App1.
- C. Configure an AppLocker policy.
- D. Configure a Software Restriction Policy.
Answer : B
Explanation:
http://www.youtube.com/watch?v=XgbjlrdkvUk
http://technet.microsoft.com/en-us/library/dd837645(v=ws.10).aspx
Question 9
The help desk reports that they receive many calls from remote users who cannot access
Internet Web sites while they are connected to the VPN. The help desk instructs the users to manually configure the VPN connection so that the users can access Internet Web sites while connected to the VPN.
You need to provide a recommendation to reduce the number of calls to the help desk regarding this issue.
What should you recommend?
- A. Deploy a Network Policy Server (NPS).
- B. Replace the SSTP-based VPN with a PPTP-based VPN.
- C. Issue computer certificates from a trusted root certification authority (CA) to all remote users.
- D. Create and distribute Connection Manager Administration Kit (CMAK) profiles to all remote users.
Answer : D
Question 10
A group of users from office 2 travels to office 1 to work on a project. The users from office
2 report that they are unable to connect to the wireless network in office 1 from their portable computers.
A help desk administrator manually provides the users with access to the wireless network.
You need to ensure that the next time users from office 2 travel to office 1 they can connect to the wireless network in office 1.
What should you request?
- A. Link GPO1 to Office2-Users-OU.
- B. Link GPO1 to Office2-Computers-OU.
- C. Change the office attribute for the user accounts.
- D. Change the location attribute for the computer accounts.
Answer : B
Question 11
A user's computer fails. The help desk provides the user with a new computer. The user's
Documents folder is restored from the backup.
The user reports that he can no longer access his encrypted files. The help desk recovers the files by using a data recovery agent (DRA).
You need to ensure that when users receive new computers, they can access their encrypted files without administrative intervention.
What should you request?
- A. credential roaming be enabled
- B. BitLocker be enabled on all computers
- C. user accounts be trusted for delegation
- D. the CA be configured for key archival and recovery
Answer : A
Explanation:
A. credential roaming be enabled
Credential roaming allows organizations to store certificates and private keys in Active
Directory Domain -
Services (AD DS) separately from application state or configuration information.
Credential roaming uses existing logon and autoenrollment mechanisms to securely download certificates and keys to a local computer whenever a user logs on and, if desired, remove them when the user logs off. In addition, the integrity of these credentials is maintained under any conditions, such as when certificates are updated and when users log on to more than one computer at a time.
B. BitLocker be enabled on all computers
C. user accounts be trusted for delegation
This security setting determines which users can set the Trusted for Delegation setting on a user or computer object.
The user or object that is granted this privilege must have write access to the account control flags on the user or computer object. A server process running on a computer (or under a user context) that is trusted for delegation can access resources on another computer using delegated credentials of a client, as long as the client account does not have the Account cannot be delegated account control flag set.
D. the CA be configured for key archival and recovery
Question 12
An administrator modifies the external IP address of Web1 and creates a Hosts (A) record for website1.wingtiptoys.com on the external DNS servers.
Your users report that they can no longer connect to website1.wingtiptoys.com from the
Internet.
You need to ensure that users can connect to website1.wingtiptoys.com from the Internet.
What should you do?
A. Instruct the users to modify the DNS client settings on their computers.
B. Instruct the users to remove an entry from the Hosts file that is located on their computers.
C. Request that an administrator create a Pointer (PTR) resource record for the new IP address of Web1.
D. Request that an administrator create an alias (CNAME) resource record for website1.wingtiptoys.com.
Answer : B
Topic 10, Humongous Insurance
You are an enterprise desktop support technician for Humongous Insurance.
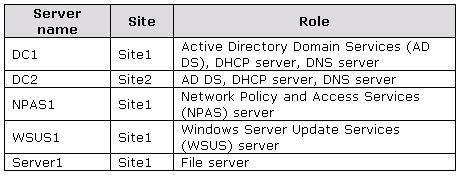
Active Directory Configuration
The company has two offices named Office1 and Office2.
The network contains an Active Directory forest named humongousinsurance.com. An
Active Directory site exists for each office. The sites are named Site1 and Site2.
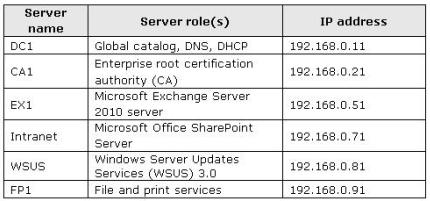
Server Configuration
All servers run Windows Server 2008 R2 and are joined to the domain. The relevant
servers are configured as shown in the following table.
Question 13
Several users in the sales department report that their user accounts are locked out shortly after they change their user passwords.
You need to minimize the number of account lockouts that occur after the users change their passwords.
What should you instruct the users to do?
- A. Delete all entries from the Credential Manager vault.
- B. Change their passwords and then create a password reset disk.
- C. Change their passwords and then configure App2 to log on by using a service account.
- D. Change their passwords and then log off and log back on to their computers.
Answer : C
Question 14
Each day, 100 users in Office2 download a 5-MB product catalog file from a share on
Server1.
The network administrator reports that the downloads cause an excessive load on the
WAN link between Office1 and Office2.
You need to recommend a solution to minimize WAN utilization. The solution must not require that additional servers be deployed.
What should you recommend?
- A. BranchCache in distributed cache mode
- B. BranchCache in hosted cache mode
- C. Distributed File System Replication (DFSR)
- D. File Server Resource Management (FSRM)
Answer : A
Question 15
Humongous Insurance users who work at Fabrikam report that when they move between different wireless networks, they are prompted to manually reconnect to the VPN.
You need to ensure that the users can automatically reconnect to the VPN when they move between wireless networks.
What should you request?
A. that a network administrator create a CNAME record named AUTODISCOVER in the humongousinsurance.com DNS zone
B. that a network administrator enable Network Load Balancing on NPAS1
C. that users use only IKEv2-based VPN connections
D. that users use only SSTP-based VPN connections
Answer : C
Topic 11, Baldwin Museum of Science
You are an enterprise desktop support technician for the Baldwin Museum of Science.
The Baldwin Museum of Science is located in Dublin. The museum has 2,000 employees.
All employees have laptop computers that have cellular connections.
The museum has a main office and three satellite offices.
Active Directory Configuration
The network contains an Active Directory forest. The forest contains a domain named
Baldwinmuseumofscience.com.
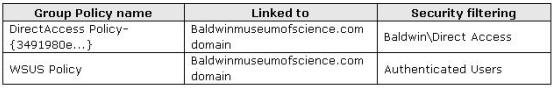
The relevant group policy information is shown in the following table.