Configuring Advanced Windows Server 2012 Services v1.0
Question 1
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2 and has the DHCP Server server role installed.
You need to create an IPv6 scope on Server1. The scope must use an address space that is reserved for private networks. The addresses must be routable.
Which IPV6 scope prefix should you use?
- A. 2001:123:4567:890A::
- B. FE80:123:4567::
- C. FF00:123:4567:890A::
- D. FD00:123:4567::
Answer : D
A unique local address (ULA) is an IPv6 address in the block fc00::/7, defined in RFC 4193. It is the approximate IPv6 counterpart of the IPv4 private address.
The address block fc00::/7 is divided into two /8 groups:
-> The block fc00::/8 has not been defined yet.
-> The block fd00::/8 is defined for /48 prefixes, formed by setting the 40 least-significant bits of the prefix to a randomly generated bit string.
Prefixes in the fd00::/8 range have similar properties as those of the IPv4 private address ranges:
-> They are not allocated by an address registry and may be used in networks by anyone without outside involvement.
-> They are not guaranteed to be globally unique.
-> Reverse Domain Name System (DNS) entries (under ip6.arpa) for fd00::/8 ULAs cannot be delegated in the global DNS.
References:
https://tools.ietf.org/html/rfc4193
Question 2
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012 R2.
DC1 has the DNS Server server role installed.
The network contains client computers that run either Linux, Windows 7, or Windows 8.1.
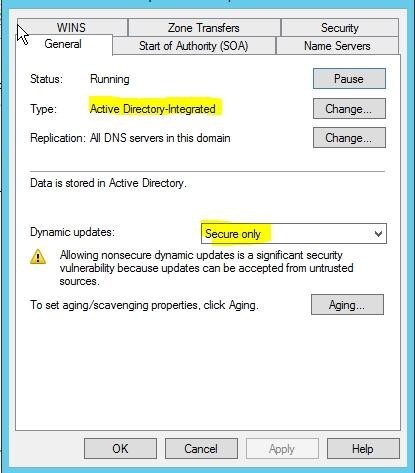
You have a standard primary zone named adatum.com as shown in the exhibit. (Click the Exhibit button.)
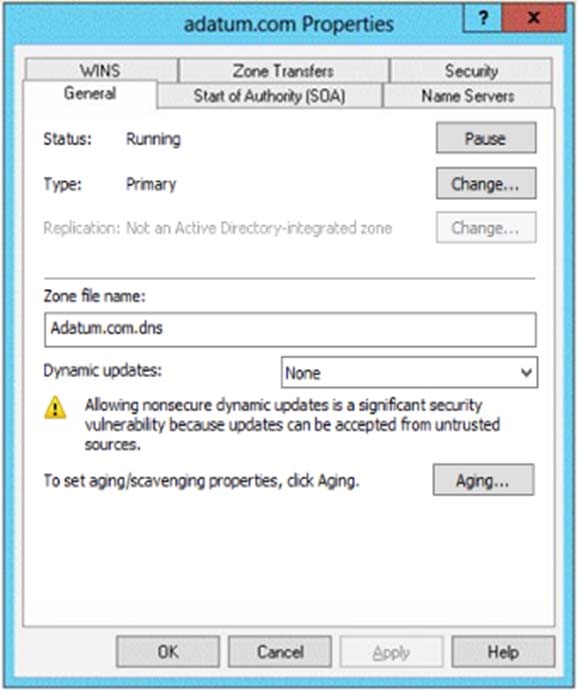
You plan to configure Name Protection on all of the DHCP servers.
You need to configure the adatum.com zone to support Name Protection.
Which two configurations should you perform from DNS Manager? (Each correct answer presents part of the solution. Choose two.)
- A. Sign the zone.
- B. Store the zone in Active Directory.
- C. Modify the Security settings of the zone.
- D. Configure Dynamic updates.
- E. Add a DNS key record
Answer : BD
Explanation:
Name protection requires secure update to work. Without name protection DNS names may be hijacked.
You can use the following procedures to allow only secure dynamic updates for a zone. Secure dynamic update is supported only for Active Directoryintegrated zones. If the zone type is configured differently, you must change the zone type and directory-integrate the zone before securing it for Domain Name System
(DNS) dynamic updates.
1. (B) Convert primary DNS server to Active Directory integrated primary
2. (D) Enable secure dynamic updates
References:
https://technet.microsoft.com/en-us/library/ee941152(v=ws.10).aspx
Question 3
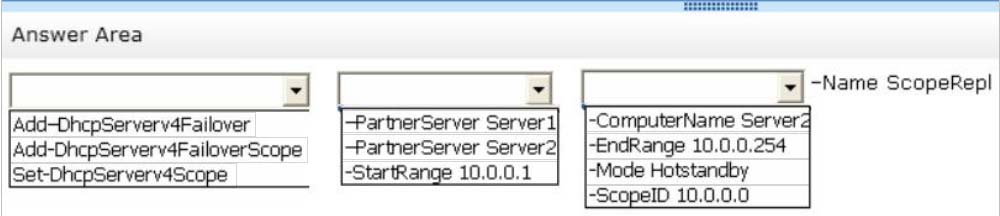
HOTSPOT -
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2. All servers run Windows
Server 2012 R2.
You install the DHCP Server server role on both servers.
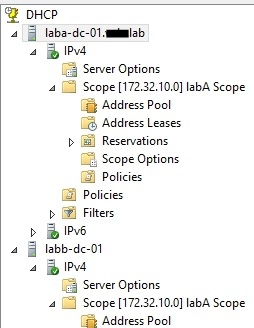
On Server1, you have the DHCP scope configured as shown in the exhibit. (Click the Exhibit button.)

You need to configure the scope to be load-balanced across Server1 and Server2.
What Windows PowerShell cmdlet should you run on Server1?
To answer, select the appropriate options in the answer area.
Hot Area:
Answer : 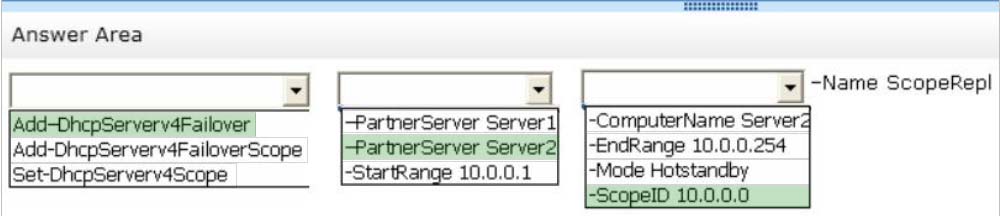
Explanation:
Add-DhcpServerv4Failover -
The Add-DhcpServerv4Failover cmdlet adds a new IPv4 failover relationship to a Dynamic Host Configuration Protocol (DHCP) server service.
-PartnerServer<String>
Specifies the IPv4 address, or host name, of the partner DHCP server service with which the failover relationship is created.
-ScopeId<IPAddress[]>
Specifies the scope identifiers, in IPv4 address format, which are to be added to the failover relationship.
Example:
References:
https://docs.microsoft.com/en-us/powershell/module/dhcpserver/add-dhcpserverv4failover
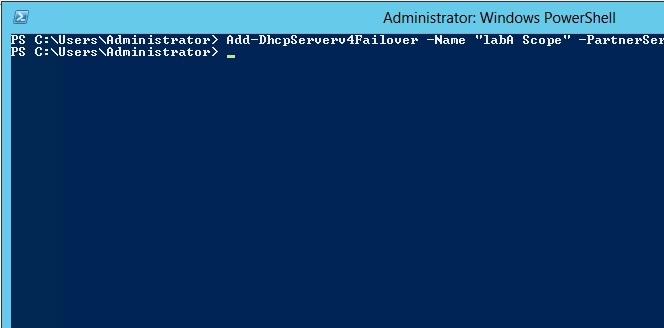
Question 4
HOTSPOT -
Your network contains an Active Directory domain named contoso.com. The domain contains two DHCP servers named Server1 and Server2. Both servers have multiple IPv4 scopes.
Server1 and Server2 are used to assign IP addresses for the network IDs of 172.20.0.0/16 and 131.107.0.0/16.
You install the IP Address Management (IPAM) Server feature on a server named IPAM1 and configure IPAM1 to manage Server1 and Server2.
Some users from the 172.20.0.0 network report that they occasionally receive an IP address conflict error message.
You need to identify whether any scopes in the 172.20.0.0 network ID conflict with one another.
What Windows PowerShell cmdlet should you run?
To answer, select the appropriate options in the answer area.
Hot Area:
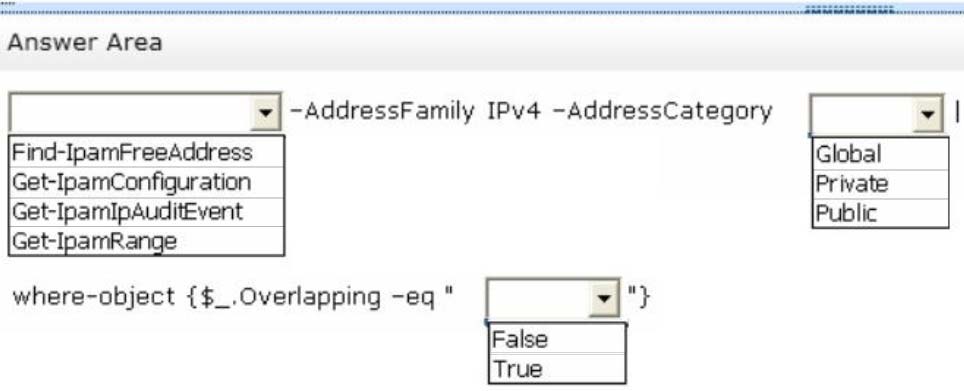
Answer : 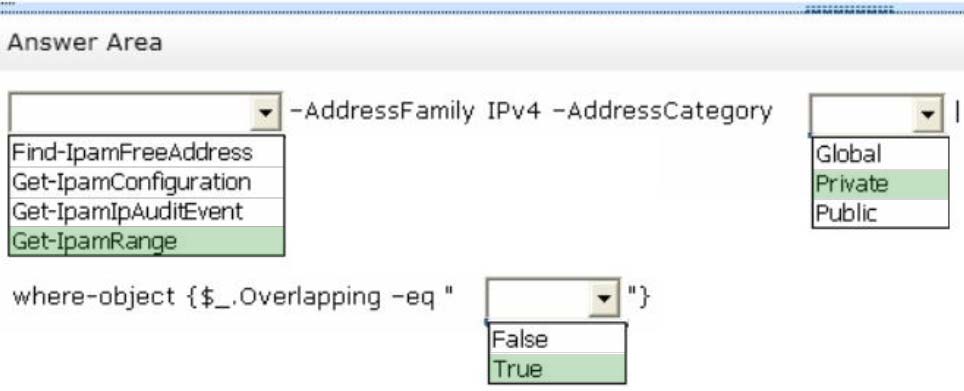
Explanation:
Type the following command at a Windows PowerShell prompt and press ENTER:
PS C:\> Get-IpamRange ""AddressFamily IPv4 ""AddressCategory Private|where-object {$_.Overlapping ""eq "True"}
The previous command will display any overlapping IP address ranges, if they exist.
References:
https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-R2-and-2012/dn268503(v=ws.11)
Question 5
Your network contains two DNS servers named DNS1 and DNS2 that run Windows Server 2012 R2.
DNS1 has a primary zone named contoso.com. DNS2 has a secondary copy of the contoso.com zone.
You need to log the zone transfer packets sent between DNS1 and DNS2.
What should you configure?
- A. Monitoring from DNS Manager
- B. Logging from Windows Firewall with Advanced Security
- C. A Data Collector Set (DCS) from Performance Monitor
- D. Debug logging from DNS Manager
Answer : D
Explanation:
Debug logging allows you to log the packets sent and received by a DNS server. Debug logging is disabled by default, and because it is resource intensive, you should only activate it temporarily when you need more specific detailed information about server performance.
Reference: Active Directory 2008: DNS Debug Logging Facts.
Question 6
Your network contains an Active Directory forest named contoso.com.
Users frequently access the website of an external partner company. The URL of the website is http://partners.adatum.com.
The partner company informs you that it will perform maintenance on its Web server and that the IP addresses of the Web server will change.
After the change is complete, the users on your internal network report that they fail to access the website. However, some users who work from home report that they can access the website.
You need to ensure that your DNS servers can resolve partners.adatum.com to the correct IP address immediately.
What should you do?
- A. Run dnscmd and specify the CacheLockingPercent parameter.
- B. Run Set-DnsServerGlobalQueryBlockList.
- C. Run ipconfig and specify the Renew parameter.
- D. Run Set-DnsServerCache.
Answer : D
Explanation:
The Set-DnsServerCache cmdlet modifies cache settings for a DomainName System (DNS) server.
Run Set-DnsServerCache with the -LockingPercent switch.
-LockingPercent<UInt32>
Specifies a percentage of the original Time to Live (TTL) value that caching can consume.
Cache locking is configured as a percent value. For example, if the cache locking value is set to 50, the DNS server does not overwrite a cached entry for half of the duration of the TTL. By default, the cache locking percent value is 100. This value means that the DNS server will not overwrite cached entries for the entire duration of the TTL.
Note. A better way would be clear the DNS cache on the DNS server with either Dnscmd /ClearCache (from command prompt), or Clear-DnsServerCache (from
Windows PowerShell).
References:
https://technet.microsoft.com/en-us/library/jj649852.aspx
Incorrect Answers:
A. You need to use the /config parameter as well:
You can change this value if you like by using the dnscmd command: dnscmd /Config /CacheLockingPercent<percent>
Question 7
You have a server named Server1.
You install the IP Address Management (IPAM) Server feature on Server1.
You need to provide a user named User1 with the ability to set the access scope of all the DHCP servers that are managed by IPAM. The solution must use the principle of least privilege.
Which user role should you assign to User1?
- A. DNS Record Administrator Role
- B. IPAM DHCP Reservations Administrator Role
- C. IPAM Administrator Role
- D. IPAM DHCP Administrator Role
Answer : D
Explanation:
The IPAM DHCP administrator role completely manages DHCP servers.
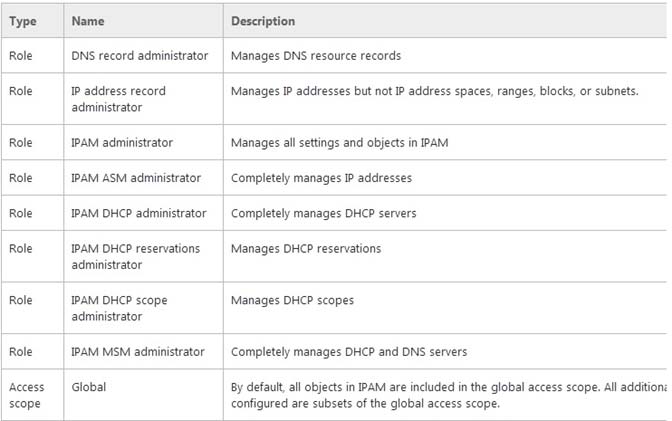
References:
https://docs.microsoft.com/en-us/windows-server/networking/technologies/ipam/what-s-new-in-ipam
Question 8
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 and a member server named
Server1. Server1 has the IP Address Management (IPAM) Server feature installed.
On Dc1, you configure Windows Firewall to allow all of the necessary inbound ports for IPAM.
On Server1, you open Server Manager as shown in the exhibit. (Click the Exhibit button.)
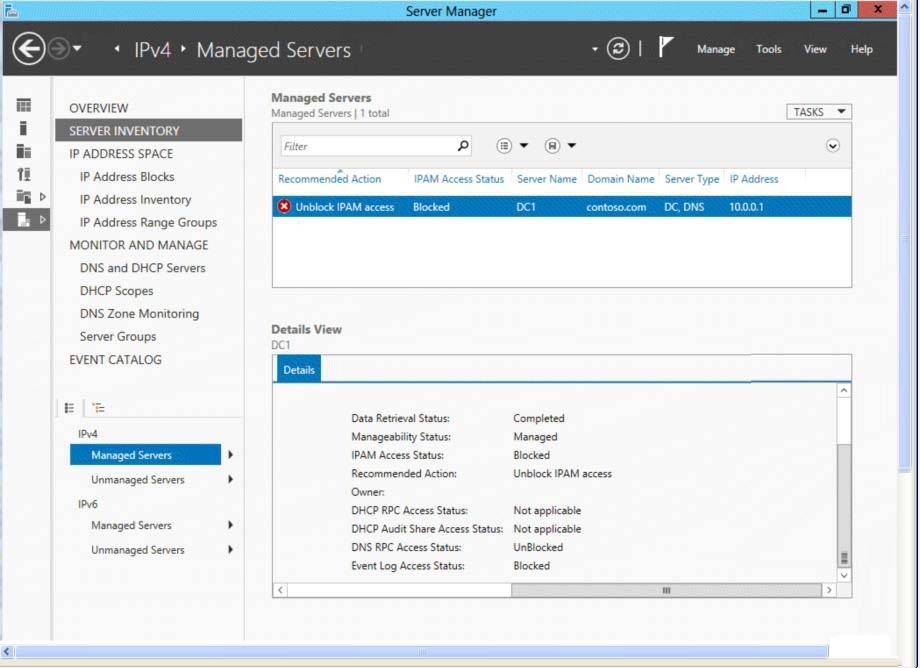
You need to ensure that you can use IPAM on Server1 to manage DNS on DC1.
What should you do?
- A. Modify the outbound firewall rules on Server1.
- B. Modify the inbound firewall rules on Server1.
- C. Add Server1 to the Remote Management Users group.
- D. Add Server1 to the Event Log Readers group.
Answer : D
Explanation:
To access configuration data and server event logs, the IPAM server must be a member of the domain IPAM Users Group (IPAMUG). The IPAM server must also be a member of the Event Log Readers security group.
Note: The computer account of the IPAM server must be a member of the Event Log Readers security group.
References:
https://technet.microsoft.com/en-us/library/jj878317.aspx
https://technet.microsoft.com/en-us/library/jj878313.aspx
Question 9
You have a server named SCI that runs a Server Core Installation of Windows Server 2012 R2. Shadow copies are enabled on all volumes.
You need to delete a specific shadow copy. The solution must minimize server downtime.
Which tool should you use?
- A. Shadow
- B. Diskshadow
- C. Wbadmin
- D. Diskpart
Answer : B
Explanation:
DiskShadow.exe is a tool that exposes the functionality offered by the Volume Shadow Copy Service (VSS).
The diskshadow command delete shadows deletes shadow copies.
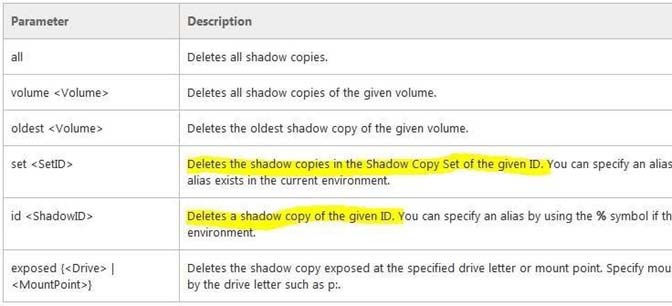
References:
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/diskshadow
Question 10
You have 20 servers that run Windows Server 2012 R2.
You need to create a Windows PowerShell script that registers each server in Microsoft Azure Backup and sets an encryption passphrase.
Which two PowerShell cmdlets should you run in the script? (Each correct answer presents part of the solution. Choose two.)
- A. New-OBPolicy
- B. New-OBRetentionPolicy
- C. Add-OBFileSpec
- D. Start-OBRegistration
- E. Set OBMachineSetting
Answer : DE
Explanation:
D. Start-OBRegistration -
Registers the current computer with Windows Azure Online Backup using the credentials (username and password) created during enrollment.
E. The Set-OBMachineSetting cmdlet sets a OBMachineSetting object for the server that includes proxy server settings for accessing the internet, network bandwidth throttling settings, and the encryption passphrase that is required to decrypt the files during recovery to another server.
Incorrect Answers:
C. TheAdd-OBFileSpec cmdlet adds the OBFileSpecobject, which specifies the items to include or exclude from a backup, to the backup policy (OBPolicyobject).
The OBFileSpecobject can include or exclude multiple files, folders, or volumes. T
References:
https://technet.microsoft.com/en-us/library/hh770398.aspx
https://technet.microsoft.com/en-us/library/hh770409.aspx
Question 11
You have 30 servers that run Windows Server 2012 R2.
All of the servers are backed up daily by using Windows Azure Backup.
You need to perform an immediate backup of all the servers to Windows Azure Backup.
Which Windows PowerShell cmdlets should you run on each server?
- A. Get-OBPolicy | StartOBBackup
- B. Start-OBRegistration | StartOBBackup
- C. Get-WBPolicy | Start-WBBackup
- D. Get-WBBackupTarget | Start-WBBackup
Answer : A
Explanation:
This example starts a backup job using a policy.
Windows PowerShell -
PS C:\> Get-OBPolicy | Start-OBBackup
Incorrect Answers:
B. Registers the current computer to Windows Azure Backup.
C. Not using Azure -
D. Not using Azure -
References:
https://technet.microsoft.com/en-us/library/hh770406(v=wps.620).aspx
Question 12
You have a server named Server1 that runs Windows Server 2012 R2 and is used for testing.
A developer at your company creates and installs an unsigned kernel-mode driver on Server1. The developer reports that Server1 will no longer start.
You need to ensure that the developer can test the new driver. The solution must minimize the amount of data loss.
Which Advanced Boot Option should you select?
- A. Disable Driver Signature Enforcement
- B. Disable automatic restart on system failure
- C. Last Know Good Configuration (advanced)
- D. Repair Your Computer
Answer : A
Explanation:
A. By default, 64-bit versions of Windows Vista and later versions of Windows will load a kernel- mode driver only if the kernel can verify the driver signature.
However, this default behavior can be disabled to facilitate early driver development and non-automated testing.
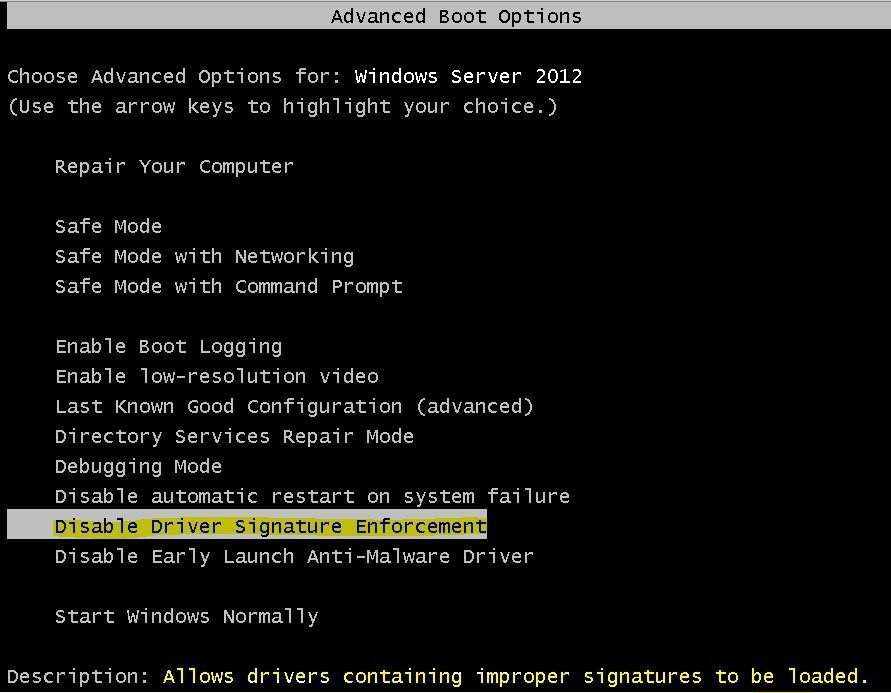
Incorrect Answers:
B. specifies that Windows automatically restarts your computer when a failure occurs.
C. Developer would not be able to test the driver as needed.
D. Removes or repairs critical windows files, Developer would not be able to test the driver as needed and some file loss.
References:
https://technet.microsoft.com/en-us/library/jj134246.aspx
http://msdn.microsoft.com/en-us/library/windows/hardware/ff547565(v=vs.85).aspx
Question 13
You have a server named Server1 that runs Windows Server 2012 R2.
When you install a custom Application on Server1 and restart the server, you receive the following error message: "The Boot Configuration Data file is missing some required information.
File: \Boot\BCD -
Error code: 0x0000034."
You start Server1 by using Windows RE.
You need to ensure that you can start Windows Server 2012 R2 on Server1.
Which tool should you use?
- A. Bootsect
- B. Bootim
- C. Bootrec
- D. Bootcfg
Answer : C
Explanation:
Bootrec.exe tool to troubleshoot "Bootmgr Is Missing" issue. The /ScanOs option scans all disks for installations that are compatible with Windows Vista or
Windows 7. Additionally, this option displays the entries that are currently not in the BCD store. Use this option when there are Windows Vista or Windows 7 installations that the Boot Manager menu does not list.
Error code 0x0000034 while booting.
Resolution:
Put the Windows Windows 7 installation disc in the disc drive, and then start the computer.
Press any key when the message indicating "Press any key to boot from CD or DVD ...". appears.
Select a language, time, currency, and a keyboard or another input method. Then click Next.
Click Repair your computer.
Click the operating system that you want to repair, and then click Next.
In the System Recovery Options dialog box, click Command Prompt.
Type Bootrec /RebuildBcd, and then press ENTER.
Incorrect Answers:
A. Bootsect.exe updates the master boot code for hard disk partitions to switch between BOOTMGR and NTLDR. You can use this tool to restore the boot sector on your computer. This tool replaces FixFAT and FixNTFS.
D. The bootcfg command is a Microsoft Windows Server 2003 utility that modifies the Boot.ini file.
References:
https://technet.microsoft.com/en-us/library/cc749177(v=ws.10).aspx http://support.microsoft.com/kb/927392/en-us http://answers.microsoft.com/en-us/windows/forum/windows_7-system/error-code-0x0000034-in- windows-7/4dcb8d38-a206-40ed-bced-55e4a4de9bf2
Question 14
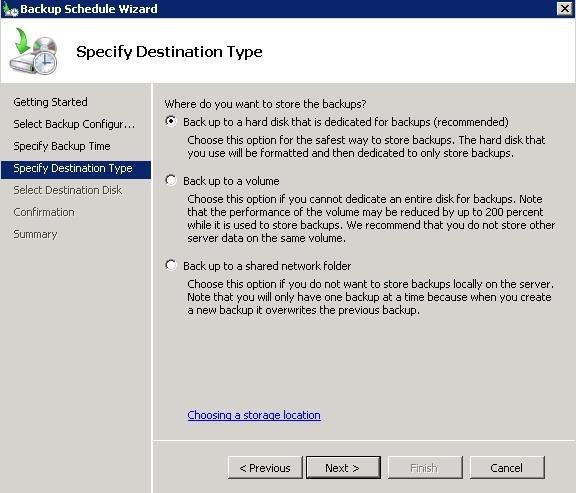
You have a server named Server1 that runs Windows Server 2012 R2. Server1 is backed up by using Windows Server Backup. The backup configuration is shown in the exhibit. (Click the Exhibit button.)
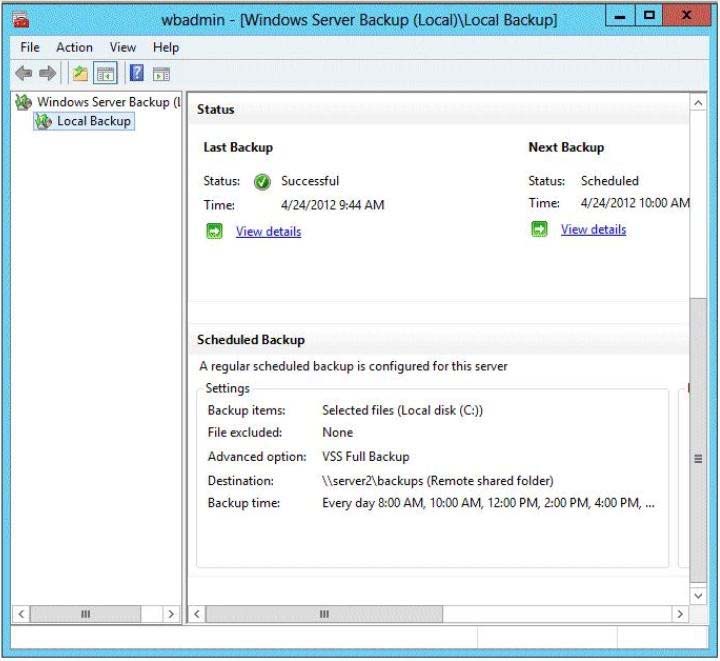
You discover that only the last copy of the backup is maintained.
You need to ensure that multiple backup copies are maintained.
What should you do?
- A. Modify the backup destination.
- B. Configure the Optimize Backup Performance settings.
- C. Modify the Volume Shadow Copy Service (VSS) settings.
- D. Modify the backup times.
Answer : A
Explanation:
The destination in the exhibit shows a network share is used. If a network share is being used only the latest copy will be saved
References:
http://windows.microsoft.com/en-us/windows7/where-should-i-save-my-backup
Question 15
Your network contains an Active Directory domain named contoso.com. The domain contains four servers named Server1, Server2, Server3, and Server4 that run
Windows Server 2012 R2. All servers have the Hyper-V server role and the Failover Clustering feature installed.
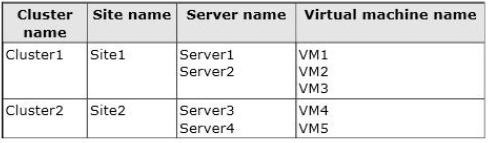
You need to replicate virtual machines from Cluster1 to Cluster2.
Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.)
- A. From Hyper-V Manager on a node in Cluster2, create three virtual machines.
- B. From Cluster2, add and configure the Hyper-V Replica Broker role.
- C. From Failover Cluster Manager on Cluster1, configure each virtual machine for replication.
- D. From Cluster1, add and configure the Hyper-V Replica Broker role.
- E. From Hyper-V Manager on a node in Cluster2 modify the Hyper-V settings.
Answer : CDE
Explanation:
D. You must configure the Hyper-V Replica Broker for cluster1.
E. We must configure configure the Replica server to receive replication from primary servers:
-> In Hyper-V Manager, click Hyper-V Settings in the Actions pane.
-> In the Hyper-V Settings dialog, click Replication Configuration.
-> In the Details pane, select Enable this computer as a Replica server.
C. Enable virtual machine replication.
Once the hosting server is configured for Replica, you can enable replication for each virtual machine that you want to be replicated.
References:
https://technet.microsoft.com/en-us/library/jj134207.aspx