Certified Ethical Hacker v10 Exam v1.0
Question 1
Steve, a scientist who works in a governmental security agency, developed a technological solution to identify people based on walking patterns and implemented this approach to a physical control access.
A camera captures people walking and identifies the individuals using Steve"™s approach.
After that, people must approximate their RFID badges. Both the identifications are required to open the door.
In this case, we can say:
- A. Although the approach has two phases, it actually implements just one authentication factor
- B. The solution implements the two authentication factors: physical object and physical characteristic
- C. The solution will have a high level of false positives
- D. Biological motion cannot be used to identify people
Answer : B
Question 2
Which Intrusion Detection System is the best applicable for large environments where critical assets on the network need extra scrutiny and is ideal for observing sensitive network segments?
- A. Honeypots
- B. Firewalls
- C. Network-based intrusion detection system (NIDS)
- D. Host-based intrusion detection system (HIDS)
Answer : C
Question 3
Which of the following is a serious vulnerability in the popular OpenSSL cryptographic software library? This weakness allows stealing the information protected, under normal conditions, by the SSL/TLS encryption used to secure the Internet.
- A. SSL/TLS Renegotiation Vulnerability
- B. Shellshock
- C. Heartbleed Bug
- D. POODLE
Answer : C
Question 4
Which protocol is used for setting up secure channels between two devices, typically in VPNs?
- A. PPP
- B. IPSEC
- C. PEM
- D. SET
Answer : B
Question 5
Which of the following Secure Hashing Algorithm (SHA) produces a 160-bit digest from a message with a maximum length of (264-1) bits and resembles the MD5 algorithm?
- A. SHA-2
- B. SHA-3
- C. SHA-1
- D. SHA-0
Answer : C
Question 6
When does the Payment Card Industry Data Security Standard (PCI-DSS) require organizations to perform external and internal penetration testing?
- A. At least twice a year or after any significant upgrade or modification
- B. At least once a year and after any significant upgrade or modification
- C. At least once every two years and after any significant upgrade or modification
- D. At least once every three years or after any significant upgrade or modification
Answer : B
Question 7
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is unreachable, ICMP may be disabled and the network may be using TCP. Which other option could the tester use to get a response from a host using TCP?
- A. Traceroute
- B. Hping
- C. TCP ping
- D. Broadcast ping
Answer : B
Question 8
Which of the following types of jailbreaking allows user-level access but does not allow iboot-level access?
- A. Bootrom Exploit
- B. iBoot Exploit
- C. Sandbox Exploit
- D. Userland Exploit
Answer : D
Question 9
What is not a PCI compliance recommendation?
- A. Use a firewall between the public network and the payment card data.
- B. Use encryption to protect all transmission of card holder data over any public network.
- C. Rotate employees handling credit card transactions on a yearly basis to different departments.
- D. Limit access to card holder data to as few individuals as possible.
Answer : C
Question 10
The "white box testing" methodology enforces what kind of restriction?
- A. Only the internal operation of a system is known to the tester.
- B. The internal operation of a system is completely known to the tester.
- C. The internal operation of a system is only partly accessible to the tester.
- D. Only the external operation of a system is accessible to the tester.
Answer : B
Question 11
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.
- A. SQL injection attack
- B. Cross-Site Scripting (XSS)
- C. LDAP Injection attack
- D. Cross-Site Request Forgery (CSRF)
Answer : B
Question 12
This tool is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, as well as the PTW attack, thus making the attack much faster compared to other WEP cracking tools.
Which of the following tools is being described?
- A. wificracker
- B. Airguard
- C. WLAN-crack
- D. Aircrack-ng
Answer : D
Question 13
The following is part of a log file taken from the machine on the network with the IP address of 192.168.0.110:
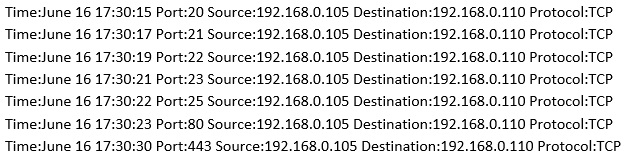
What type of activity has been logged?
- A. Teardrop attack targeting 192.168.0.110
- B. Denial of service attack targeting 192.168.0.105
- C. Port scan targeting 192.168.0.110
- D. Port scan targeting 192.168.0.105
Answer : C
Question 14
You are attempting to run an Nmap port scan on a web server. Which of the following commands would result in a scan of common ports with the least amount of noise in order to evade IDS?
- A. nmap -A - Pn
- B. nmap -sP -p-65535 -T5
- C. nmap -sT -O -T0
- D. nmap -A --host-timeout 99 -T1
Answer : C
Question 15
Bob, your senior colleague, has sent you a mail regarding aa deal with one of the clients. You are requested to accept the offer and you oblige.
After 2 days, Bob denies that he had ever sent a mail.
What do you want to "know" to prove yourself that it was Bob who had send a mail?
- A. Confidentiality
- B. Integrity
- C. Non-Repudiation
- D. Authentication
Answer : C