Threat Prevention v6.0
Question 1
In SmartViewTracker, you see a log record of type control and severity critical for the product Threat Emulation which says: cloud emulation failed. Reason: failed to authenticate gateway...
What is likely to be the reason for this failure?
- A. The user provided the wrong credentials to the gateway
- B. The gateway should be configured in a way that Threat Emulation can be done locally in case the cloud is not accessible
- C. The cloud is not accessible right now
- D. Verify the gateway license / contract
Answer : D
Question 2
Check Point Intrusion Prevention System (IPS) is available in two deployment methods, as a blade and also a dedicated appliance. What is the dedicated appliance called?
- A. InterSpect Appliance
- B. IPS-1 Sensor
- C. Smart-1 Appliance
- D. Power-1 Appliance
Answer : B
Question 3
Which of these statements describes the Check Point ThreatCloud?
- A. A worldwide collaborative security network
- B. Prevents vulnerability exploits
- C. Controls access to web sites based on category
- D. Blocks or limits usage of web applications
Answer : A
Question 4
Which of the following is information shared via ThreatCloud?
- A. Sensitive Corporate Data
- B. Bot and virus signatures
- C. Anticipated Attack Methods
- D. Compromised Machine IP Addresses
Answer : B
Question 5
When pushing the Threat Prevention policy, which of the following blades will NOT get updated?
- A. IPS
- B. Threat Emulation
- C. Anti-Bot
- D. Anti-Virus
Answer : A
Question 6
IPS is primarily a __________-based engine.
- A. Signature
- B. Difference
- C. Action
- D. Anomaly
Answer : A
Question 7
What is the minimum amount of RAM needed for a Threat Prevention Appliance?
- A. 4 GB
- B. It depends on the number of software blades enabled.
- C. 2 GB with GAiA in 32-bit mode, 4 GB with GAiA in 64-bit mode
- D. 6 GB
Answer : A
Question 8
Which of the following is a searchable database of all known threats detected by sensors around the world?
- A. ThreatCloud
- B. ThreatWiki
- C. ThreatSpect
- D. SmartLog
Answer : B
Question 9
You just enabled the IPS blade, and have downloaded the latest signature updates. You created a custom profile but you are concerned that if you push a policy it might start dropping existing connections. What should you do?
- A. Use the recommend Protection profile instead
- B. Edit your custom profile and select Detect-only for Troubleshooting mode
- C. Edit your custom profile and enable Bypass under load
- D. Use the Default protection profile instead
Answer : B
Question 10
What is the name of Check Point collaborative network that delivers real-time dynamic security intelligence to Check Point threat prevention blades?
- A. ThreatSpect
- B. ThreatWiki
- C. ThreatCloud
- D. ThreatEmulator
Answer : C
Question 11
IPS can assist in the discovery of unknown buffer overflow attacks without any pre-defined signatures.
- A. False, only the Threat Emulator blade can discover unknown attacks.
- B. True, if Zero-Day vulnerability is enabled.
- C. False, IPS needs predefined signatures for all functions.
- D. True, if Malicious Code Protector is enabled in IPS.
Answer : D
Question 12
Which TCP ports allow LDAP users to communicate with the Account Unit?
- A. 689 clear, or 336 encrypted
- B. 636 clear, or 389 encrypted
- C. 336 clear, or 689 encrypted
- D. 389 clear, or 636 encrypted
Answer : D
Question 13
When the feature ______________ is ON, the Gateway does not block DNS requests that were identified as malicious. Instead it sends a false response with a bogus IP address to the client.
- A. Malware DNS Blacklist
- B. Malware DNS Trap
- C. Malware DNS Sinkhole
- D. Malware DNS Blackhole
Answer : B
Question 14
Looking at these logs, what happened at 10:55?
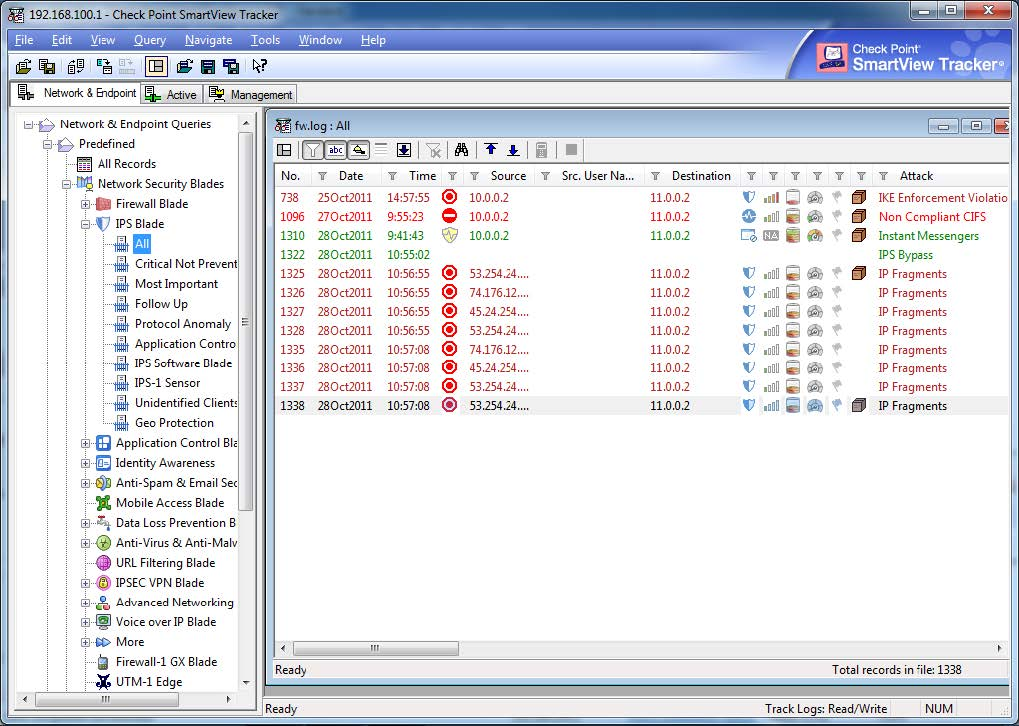
- A. An IPS rule was installed, causing IPS to temporarily stop working
- B. The Gateway was rebooted, causing IPS to temporarily stop working
- C. A new IPS policy was installed, causing IPS to temporarily stop working
- D. IPD Inspections were temporarily suspended, due to high load on the gateway
Answer : D
Question 15
Damage from a bot attack can take place after the bot compromises a machine. Which of the following represents the order by which this process takes place? The bot:
- A. infects a machine, communicates with its command and control handlers, and penetrates the organization.
- B. penetrates the organization, infects a machine, and communicates with its command and control handlers.
- C. communicates with its command and control handlers, infects a machine, and penetrates the organization.
- D. penetrates the organization, communicates with its command and control handlers, and infects a machine.
Answer : B