Check Point Certified Security Administrator (CCSA R80) v1.0
Question 1
Examine the following Rule Base.
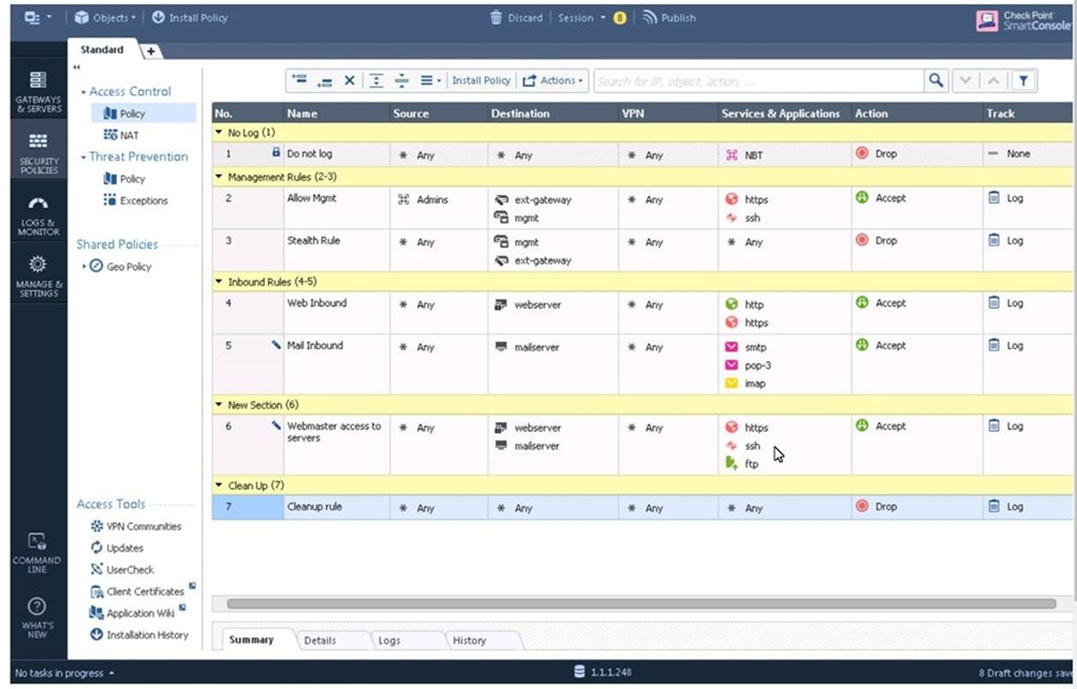
What can we infer about the recent changes made to the Rule Base?
- A. Rule 7 was created by the 'admin' administrator in the current session
- B. 8 changes have been made by administrators since the last policy installation
- C. Te rules 1, 5 and 6 cannot be edited by the 'admin' administrator
- D. Rule 1 and object webserver are locked by another administrator
Answer : D
Explantation:
On top of the print screen there is a number "8" which consists for the number of changes made and not saved.
Session Management Toolbar (top of SmartConsole)
Reference:
https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/117948
Question 2
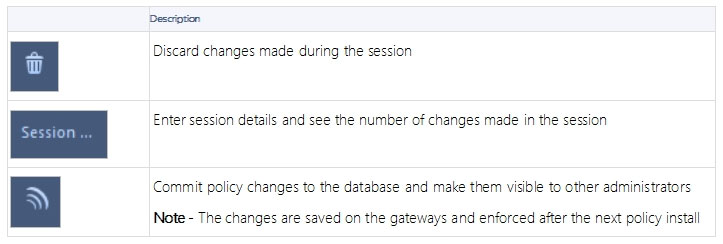
ALPHA Corp has a new administrator who logs into the Gaia Portal to make some changes. He realizes that even though he has logged in as an administrator, he is unable to make any changes because all configuration options are greyed out as shown in the screenshot image below. What is the likely cause for this?
- A. The Gaia /bin/confd is locked by another administrator from a SmartConsole session.
- B. The database is locked by another administrator SSH session.
- C. The Network address of his computer is in the blocked hosts.
- D. The IP address of his computer is not in the allowed hosts.
Answer : B
Explanation:
There is a lock on top left side of the screen. B is the logical answer.
Question 3
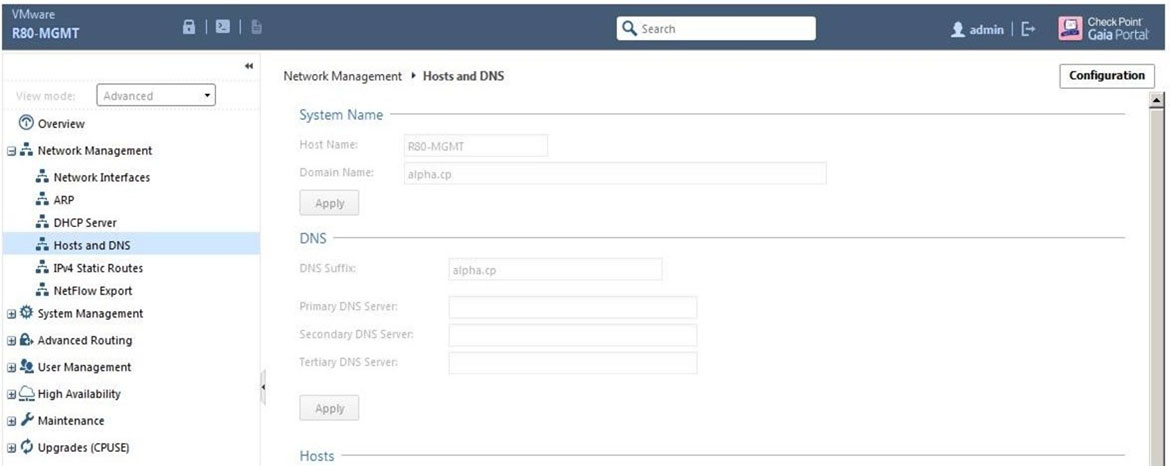
Administrator Kofi has just made some changes on his Management Server and then clicks on the Publish button in SmartConsole but then gets the error message shown in the screenshot below.
Where can the administrator check for more information on these errors?
- A. The Log and Monitor section in SmartConsole
- B. The Validations section in SmartConsole
- C. The Objects section in SmartConsole
- D. The Policies section in SmartConsole
Answer : B
Explanation:
Validation Errors -
The validations pane in SmartConsole shows configuration error messages. Examples of errors are object names that are not unique, and the use of objects that are not valid in the Rule Base.
To publish, you must fix the errors.
Reference:
https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_R80_SecMGMT/126197
Question 4
You are working with multiple Security Gateways enforcing an extensive number of rules. To simplify security administration, which action would you choose?
- A. Eliminate all possible contradictory rules such as the Stealth or Cleanup rules.
- B. Create a separate Security Policy package for each remote Security Gateway.
- C. Create network objects that restrict all applicable rules to only certain networks.
- D. Run separate SmartConsole instances to login and configure each Security Gateway directly.
Answer : B
Question 5
Harriet wants to protect sensitive information from intentional loss when users browse to a specific URL: https://personal.mymail.com, which blade will she enable to achieve her goal?
- A. DLP
- B. SSL Inspection
- C. Application Control
- D. URL Filtering
Answer : A
Explanation:
Check Point revolutionizes DLP by combining technology and processes to move businesses from passive detection to active Data Loss Prevention. Innovative
MultiSpectג„¢ data classification combines user, content and process information to make accurate decisions, while UserCheckג„¢ technology empowers users to remediate incidents in real time. Check Pointג€™s self-educating network-based DLP solution frees IT/security personnel from incident handling and educates users
ג€"
on proper data handling policies
protecting sensitive corporate information from both intentional and unintentional loss.
Reference:
https://www.checkpoint.com/downloads/product-related/datasheets/DLP-software-blade-datasheet.pdf
Question 6
To optimize Rule Base efficiency the most hit rules should be where?
- A. Removed from the Rule Base.
- B. Towards the middle of the Rule Base.
- C. Towards the top of the Rule Base.
- D. Towards the bottom of the Rule Base.
Answer : C
Explanation:
It is logical that if lesser rules are checked for the matched rule to be found the lesser CPU cycles the device is using. Checkpoint match a session from the first rule on top till the last on the bottom.
Question 7
Which of the following is NOT a license activation method?
- A. SmartConsole Wizard
- B. Online Activation
- C. License Activation Wizard
- D. Offline Activation
Answer : A
Question 8
Which policy type has its own Exceptions section?
- A. Thread Prevention
- B. Access Control
- C. Threat Emulation
- D. Desktop Security
Answer : A
Explanation:
The Exceptions Groups pane lets you define exception groups. When necessary, you can create exception groups to use in the Rule Base. An exception group contains one or more defined exceptions. This option facilitates ease-of-use so you do not have to manually define exceptions in multiple rules for commonly required exceptions. You can choose to which rules you want to add exception groups. This means they can be added to some rules and not to others, depending on necessity.
Reference:
https://sc1.checkpoint.com/documents/R77/CP_R77_ThreatPrevention_WebAdmin/82209.htm#o97030
Question 9
By default, which port does the WebUI listen on?
- A. 80
- B. 4434
- C. 443
- D. 8080
Answer : C
Explanation:
To configure Security Management Server on Gaia:
✑ Open a browser to the WebUI: https://<Gaia management IP address>
Reference:
https://sc1.checkpoint.com/documents/R80/CP_R80_Gaia_IUG/html_frameset.htm?topic=documents/R80/CP_R80_Gaia_IUG/132120
Question 10
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
- A. None, Security Management Server would be installed by itself.
- B. SmartConsole
- C. SecureClient
- D. Security Gateway
Answer : D
Explanation:
There are different deployment scenarios for Check Point software products.
✑ Standalone Deployment - The Security Management Server and the Security Gateway are installed on the same computer or appliance.
Reference:
https://sc1.checkpoint.com/documents/R76/CP_R76_Installation_and_Upgrade_Guide-webAdmin/86429.htm
Question 11
Which options are given on features, when editing a Role on Gaia Platform?
- A. Read/Write, Read Only
- B. Read/Write, Read Only, None
- C. Read/Write, None
- D. Read Only, None
Answer : B
Explanation:
Roles -
Role-based administration (RBA) lets you create administrative roles for users. With RBA, an administrator can allow Gaia users to access specified features by including those features in a role and assigning that role to users. Each role can include a combination of administrative (read/write) access to some features, monitoring (read-only) access to other features, and no access to other features.
You can also specify which access mechanisms (WebUI or the CLI) are available to the user.

Note - When users log in to the WebUI, they see only those features that they have read-only or read/write access to. If they have read-only access to a feature, they can see the settings pages, but cannot change the settings.
Gaia includes these predefined roles:
✑ adminRole - Gives the user read/write access to all features.
✑ monitorRole- Gives the user read-only access to all features.
You cannot delete or change the predefined roles.

Note - Do not define a new user for external users. An external user is one that is defined on an authentication server (such as RADIUS or TACACS) and not on the local Gaia system.
Reference:
https://sc1.checkpoint.com/documents/R77/CP_R77_Gaia_AdminWebAdminGuide/html_frameset.htm?topic=documents/R77/
CP_R77_Gaia_AdminWebAdminGuide/75930
Question 12
What is the default time length that Hit Count Data is kept?
- A. 3 month
- B. 4 weeks
- C. 12 months
- D. 1 week
Answer : A
Reference:
https://community.checkpoint.com/t5/General-Topics/What-is-the-default-time-that-HIT-count-data-is-kept-in-R80/td-p/33636
Question 13
Choose the Best place to find a Security Management Server backup file named backup_fw, on a Check Point Appliance.
- A. /var/log/Cpbackup/backups/backup/backup_fw.tgs
- B. /var/log/Cpbackup/backups/backup/backup_fw.tar
- C. /var/log/Cpbackup/backups/backups/backup_fw.tar
- D. /var/log/Cpbackup/backups/backup_fw.tgz
Answer : D
Explanation:
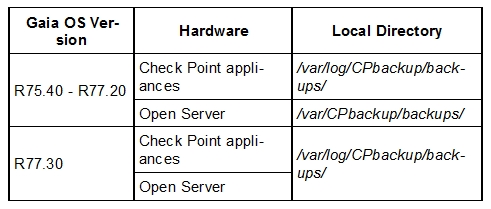
Gaia's Backup feature allows backing up the configuration of the Gaia OS and of the Security Management server database, or restoring a previously saved configuration.
The configuration is saved to a .tgz file in the following directory:
Reference:
https://supportcenter.checkpoint.com/supportcenter/portal?
action=portlets.SearchResultMainAction&eventSubmit_doGoviewsolutiondetails=&solutionid=sk91400
Question 14
With which command can you view the running configuration of Gaia Operating system?
- A. show conf-active
- B. show configuration active
- C. show configuration
- D. show running-configuration
Answer : C
Question 15
Which of the following is TRUE regarding Gaia command line?
- A. Configuration changes should be done in mgmt_cli and use CLISH for monitoring. Expert mode is used only for OS level tasks.
- B. Configuration changes should be done in expert-mode and CLISH is used for monitoring.
- C. Configuration changes should be done in mgmt_cli and use expert-mode for OS-level tasks.
- D. All configuration changes should be made in CLISH and expert-mode should be used for OS-level tasks.
Answer : D