ICND Interconnecting Cisco Networking Devices Part 1 v1.0
Question 1
Which network topology allows all traffic to flow through a central hub?
- A. bus
- B. star
- C. mesh
- D. ring
Answer : B
Explanation:
Star topology is the arrangement of the computers in such a way that all the terminals or work stations are connected to the main central hub. The terminals are referred to as the clients and the main central hub is referred to as the switch. It is the easiest way of arranging a network topology with one central main computer connected to several other functioning terminals. All the network traffic passes through the central device and all the data transmission occurs through the main switch as well as all the hub acts as the signal repeater. One advantage of such an arrangement is the simplicity and the ease with which you can add additional nodes. The disadvantage is that if an error occurs in the central hub the whole network shuts down.

Reference:
http://www.certiology.com/computing/computer-networking/network-topology.html
Question 2
Which two statements are true regarding ICMP packets? (Choose two.)
- A. They are encapsulated within IP datagrams.
- B. They guarantee datagram delivery.
- C. TRACERT uses ICMP packets.
- D. They acknowledge receipt of TCP segments.
- E. They are encapsulated within UDP datagrams.
Answer : AC
Explanation:
Ping may be used to find out whether the local machines are connected to the network or whether a remote site is reachable. This tool is a common network tool for determining the network connectivity which uses ICMP protocol instead of TCP/IP and UDP/IP. This protocol is usually associated with the network management tools which provide network information to network administrators, such as ping and traceroute (the later also uses the UDP/IP protocol).
ICMP is quite different from the TCP/IP and UDP/IP protocols. No source and destination ports are included in its packets. Therefore, usual packet-filtering rules for TCP/IP and UDP/IP are not applicable. Fortunately, a special "signature" known as the packet's Message type is included for denoting the purposes of the
ICMP packet. Most commonly used message types are namely, 0, 3, 4, 5, 8, 11, and 12 which represent echo reply, destination unreachable, source quench, redirect, echo request, time exceeded, and parameter problem respectively.
In the ping service, after receiving the ICMP "echo request" packet from the source location, the destination.
Question 3
Which method does a connected trunk port use to tag VLAN traffic?
- A. IEEE 802.1w
- B. IEEE 802.1D
- C. IEEE 802.1Q
- D. IEEE 802.1p
Answer : C
Explanation:
IEEE 802.1Q is the networking standard that supports virtual LANs (VLANs) on an Ethernet network. When a frame enters the VLAN-aware portion of the network
(a trunk link, for example), a VLAN ID tag is added to represent the VLAN membership of that frame. The picture below shows how VLAN tag is added and removed while going through the network. http://www.cisco.com/c/en/us/support/docs/lan-switching/8021q/17056-741-4.html
Question 4
On which type of device is every port in the same collision domain?
- A. a router
- B. a Layer 2 switch
- C. switch
- D. a hub
- E. a Layer 3 switch D
Answer : Explanation
Explanation:
The definition of a collision domain is a set of LAN devices whose frames could collide with one another. This happens with hubs, bridges, repeaters and wireless access points as only one device can send and receive. If more than one device tries sending or receiving, the information is lost and irrecoverable it will need to be resent. This can slow down network performance along with making it a security threat.
Question 5
Which option is the default switch port port-security violation mode?
- A. shutdown
- B. protect
- C. shutdown vlan
- D. restrict
Answer : A
Explanation:
Shutdown - This mode is the default violation mode; when in this mode, the switch will automatically force the switchport into an error disabled (err-disable) state when a violation occurs. While in this state, the switchport forwards no traffic. The switchport can be brought out of this error disabled state by issuing the errdisable recovery cause CLI command or by disabling and reenabling the switchport.
Shutdown VLAN - This mode mimics the behavior of the shutdown mode but limits the error disabled state the specific violating VLAN.
Question 6
Refer to the exhibit.
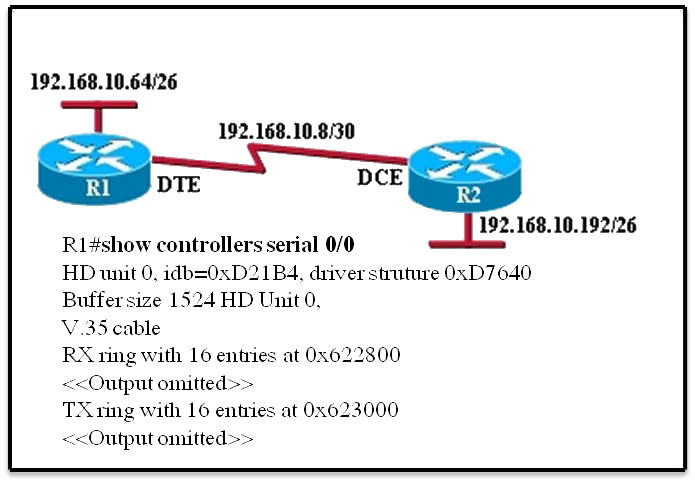
An administrator cannot connect from R1 to R2. To troubleshoot this problem, the administrator has entered the command shown in the exhibit. Based on the output shown, what could be the problem?
- A. The serial interface is configured for the wrong frame size.
- B. The serial interface does not have a cable attached.
- C. The serial interface has the wrong type of cable attached.
- D. The serial interface has a full buffer.
- E. The serial interface is configured for half duplex. C
Answer : Explanation
Explanation:
Since the output is not forthcoming it shows that the type of cable attached is wrong, though the cable is connected since it shows the cable type. According to the figure DTE cable should connect to R1 on interface but while examining using show controllers serial 0/0 command it showing that a DCE is connected so the wrong type of cable is being used.
Question 7
Which statement about native VLAN traffic is true?
- A. Cisco Discovery Protocol traffic travels on the native VLAN by default.
- B. Traffic on the native VLAN is tagged with 1 by default.
- C. Control plane traffic is blocked on the native VLAN.
- D. The native VLAN is typically disabled for security reasons.
Answer : A
Explanation:
The native VLAN is the VLAN that is configured for packets that don"™t have a tag. The default native VLAN on all Cisco Switches is VLAN 1. It is always enabled by default. These settings can all be changed: That is: you can designate a different VLAN as the native VLAN, disable VLAN 1, etc. Knowing that, we can eliminate D) as the correct answer because it is enabled by default. We can also eliminate B) because Native VLAN packets don"™t get tags by default (you can change this). Finally, Control Plane traffic is never blocked on Native VLAN 1, and even if you change the Native VLAN, the control plane traffic still comes across
VLAN 1.
Question 8
Which value is indicated by the next hop in a routing table?
- A. preference of the route source
- B. IP address of the remote router for forwarding the packets
- C. how the route was learned
- D. exit interface IP address for forwarding the packets
Answer : B
Explanation:
From official Odom cisco book is Routes for remote subnets typically list both an outgoing interface and next-hop router IP address. Routes for subnets that connect directly to the router list only the outgoing interface, because packets to these destinations do not need to be sent to another router.
Question 9
Which component of the routing table ranks routing protocols according to their preferences?
- A. administrative distance
- B. next hop
- C. metric
- D. routing protocol code
Answer : A
Explanation:
Administrative distance - This is the measure of trustworthiness of the source of the route. If a router learns about a destination from more than one routing protocol, administrative distance is compared and the preference is given to the routes with lower administrative distance. In other words, it is the believability of the source of the route.
Question 10
At which layer of the OSI model does the protocol that provides the information that is displayed by the show cdp neighbors command operate?
- A. data link
- B. application
- C. network
- D. transport
- E. physical
Answer : A
Explanation:
CDP is a device discovery protocol that runs over Layer 2 (the data link layer) on all Cisco-manufactured devices (routers, bridges, access servers, and switches) and allows network management applications to discover Cisco devices that are neighbors of already known devices.
With CDP, network management applications can learn the device type and the Simple Network Management Protocol (SNMP) agent address of neighboring devices running lower-layer, transparent protocols.
Question 11
Which statement about unicast frame forwarding on a switch is true?
- A. The TCAM table stores destination MAC addresses.
- B. If the destination MAC address is unknown, the frame is flooded to every port that is configured in the same VLAN except on the port that it was received on.
- C. The CAM table is used to determine whether traffic is permitted or denied on a switch.
- D. The source address is used to determine the switch port to which a frame is forwarded. B
Answer : Explanation
Question 12
By default, how many MAC addresses are permitted to be learned on a switch port with port-security enabled?
- A. 8
- B. 2
- C. 1
- D. 0
Answer : C
Reference:
http://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/12-2SX/configuration/guide/book/port_sec.pdf
Question 13
Which dynamic routing protocol uses only the hop count to determine the best path to a destination?
- A. IGRP
- B. RIP
- C. EIGRP
- D. OSPF
Answer : B
Explanation:
Determining the best path involves the evaluation of multiple paths to the same destination network and selecting the optimum or shortest path to reach that network. Whenever multiple paths to the same network exist, each path uses a different exit interface on the router to reach that network.
The best path is selected by a routing protocol based on the value or metric it uses to determine the distance to reach a network. A metric is the quantitative value used to measure the distance to a given network. The best path to a network is the path with the lowest metric.
Dynamic routing protocols typically use their own rules and metrics to build and update routing tables. The routing algorithm generates a value, or a metric, for each path through the network. Metrics can be based on either a single characteristic or several characteristics of a path. Some routing protocols can base route selection on multiple metrics, combining them into a single metric. The following lists some dynamic protocols and the metrics they use:
Routing Information Protocol (RIP): Hop count
Open Shortest Path First (OSPF): Cisco routers use a cost based on cumulative bandwidth from source to destination
Enhanced Interior Gateway Routing Protocol (EIGRP): Bandwidth, delay, load, reliability
Question 14
Refer to the exhibit.

The exhibit is showing the topology and the MAC address table. Host A sends a data frame to host D. Which option describes what the switch will do when it receives the frame from host A?
- A. The switch will flood the frame out of all ports except for port Fa0/3.
- B. The switch will add the destination address of the frame to the MAC address table and forward the frame to host D.
- C. The switch will add the source address and port to the MAC address table and forward the frame to host D.
- D. The switch will discard the frame and send an error message back to host A.
Answer : C
Explanation:
When switch receives the data frame from the host not having the MAC address already on the MAC table, it will add the MAC address to source port on MAC address table and sends the data frame.
Question 15
Refer to the exhibit.

If the resume command is entered after the sequence that is shown in the exhibit, which router prompt will be displayed?
- A. Router2#
- B. Router2>
- C. Router1#
- D. Router1>
Answer : B
Explanation:
If the enter command is issued the session will resume back to what it was, which is the Router2> prompt.